KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







DHS CISA and the FBI today shared more info on how an Iranian state-sponsored hacking group was able to harvest voter registration info from U.S. state websites, including election sites.
The harvested data was later used fake Proud Boys voter intimidation emails that targeted Democratic voters attempting to convince them to vote for President Trump.
“Further evaluation by CISA and the FBI has identified the targeting of U.S. state election websites was an intentional effort to influence and interfere with the 2020 U.S. presidential election,” a joint advisory published today says.
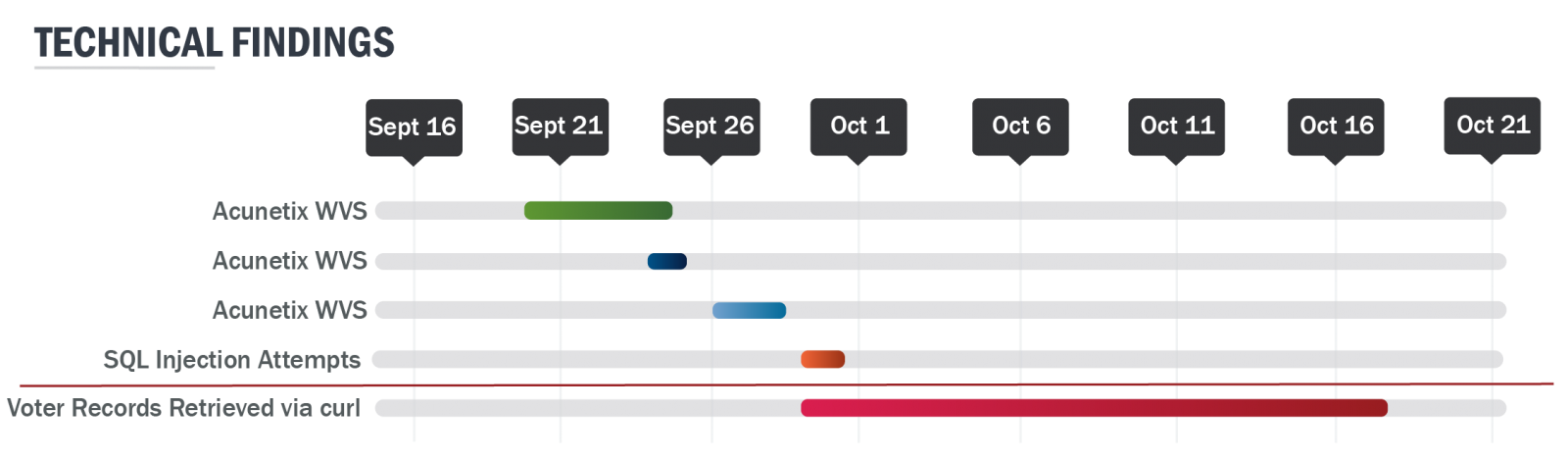
The attempts to download voter info from election websites took place between September 29 and October 17, 2020, according to the advisory.
Also Read: A Look at the Risk Assessment Form Singapore Government Requires
“This includes attempted exploitation of known vulnerabilities, directory traversal, Structured Query Language (SQL) injection, web shell uploads, and leveraging unique flaws in websites,” the FBI and CISA explain.
The advisory provides technical details regarding DNI John Ratcliffe’s confirmation during a press conference that nation state-backed Iranian hackers collected voter registration info that was used in the fake Proud Boys threatening emails.
The Iranian APT actors first used the Acunetix vulnerability scanner to detect security flaws affecting the targeted sites which later allowed them to exploit insecure servers.
Their attacks allowed them to successfully downloaded voter registration data for at least one U.S. state by exploiting election site misconfiguration and vulnerabilities.
To do that they used scripts designed to use “the cURL tool to iterate through voter records” to automatically go through databases and download them using the
“Following the review of web server access logs, CISA analysts, in coordination with the FBI, found instances of the cURL and FDM User Agents sending GET requests to a web resource associated with voter registration data,” the advisory says.
“Suspected scripted activity submitted several hundred thousand queries iterating through voter identification values, and retrieving results with varying levels of success.”
As the FBI said in a flash alert issued yesterday, many of the IP addresses used by the Iranian hackers in the fake Proud Boys email campaign are from the NordVPN service and may also correspond to other VPN providers including CDN77, HQSERV, and M247.
“While this creates the potential for false positives, any activity on the below would likely warrant further investigation,” the FBI said.
Also Read: How to Send Mass Email Without Showing Addresses: 2 Great Workarounds
During the investigation, the FBI also found evidence indicating that the APT actor researched the following info during their efforts to scan for and exploit state election sites:
FBI and CISA also provide the following general mitigation measures to block future attacks: