KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The Federal Bureau of Investigation (FBI) shared indicators of compromise (IOCs) associated with the Iranian state-sponsored threat group behind last week’s Proud Boys voter intimidation emails that targeted Democratic voters.
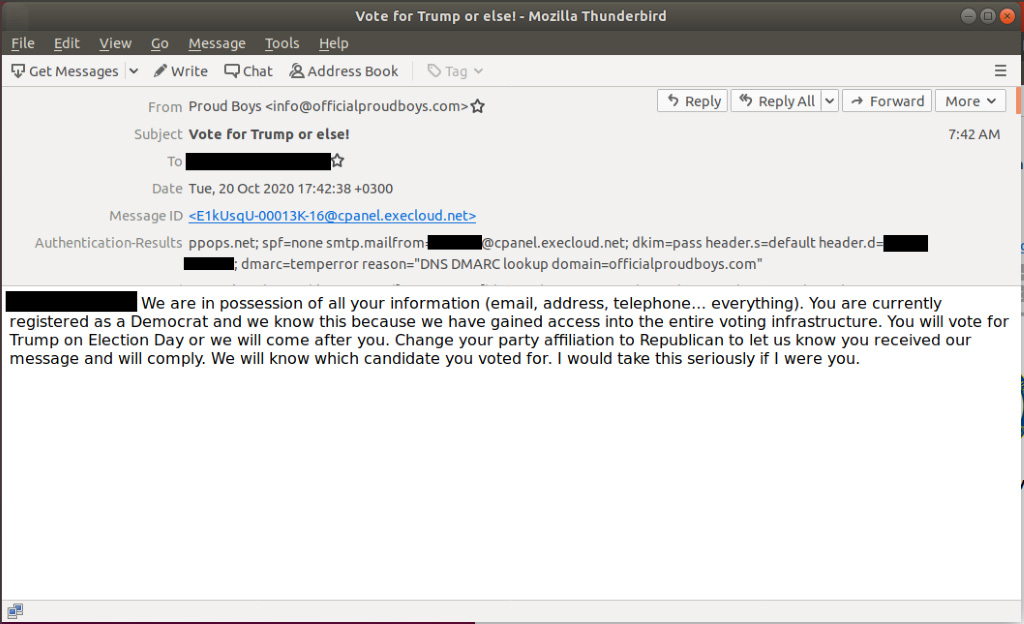
The threatening spoofed emails used the “Vote for Trump or Else” subject and warned voters registered as Democrats that they must vote for President Trump and change their party to Republican unless they want the Proud Boys far-right group to come after them.
Many of the IP addresses used in the fake Proud Boys email campaign are from the NordVPN service according to an FBI TLP:WHITE flash alert issued yesterday.
Some of the emails also included voters’ full names and mailing addresses (allegedly obtained from hacked voter registration sites) or a video showing Proud Boys hackers breaching voter registration databases.
Director of National Intelligence (DNI) John Ratcliffe confirmed in a press conference that Iranian threat actors obtained voter registration info that was used in this malicious email campaign.
The hackers’ end goals include influencing and interfering with the U.S. elections, intimidating voters, and inciting social unrest.
“While the video alone does not necessarily validate whether the actors successfully conducted a SQL injection against US election infrastructure and/or obtained voter information, it should be assumed that this group is familiar with traditional TTPs such as SQL injection and other exploitation methods referenced in AA20-296B,” the FBI says in the flash alert.
Also Read: Advisory Guidelines on Key Concepts in the PDPA: 23 Chapters
“While there is reason to doubt the veracity of the activity portrayed in the video, the FBI advises this group is likely capable of exploiting US Web sites with common vulnerabilities.”
On the same day, the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI issued a joint security advisory with details on the Iranian advanced persistent threat (APT) actors’ distributed denial-of-service (DDoS), spear-phishing, and disinformation campaigns.
Now, the FBI has shared identified IP addresses the Iranian hackers used “to conduct operations aimed at impacting the 2020 US Presidential Election, to include voter intimidation emails and dissemination of US election-related propaganda.”
Many of these IPs included in the list of IOCs correspond to paid Virtual Private Network (VPN) services that can also be used by individuals not involved with this attack campaign.
“While this creates the potential for false positives, any activity on the below would likely warrant further investigation,” the FBI adds.
Some of these VPN IPs linked to the Iranian APT actors are from NordVPN’s server list and may also correspond to other VPN providers such as CDN77, HQSERV, and M247.
The full list of IP addresses associated with the fake Proud Boys intimidation email campaign is included at the end of the FBI flash alert.
CISA and the FBI have also warned last week that a Russian state-backed APT threat group known as Energetic Bear (aka Dragonfly and Crouching Yeti) has stolen data from breached U.S. government networks during the last two months.
Also Read: Letter of Consent MOM: Getting the Details Right
The FBI also issued another flash alert earlier this week warning of hackers stealing data from U.S. government agencies and enterprise orgs via insecure SonarQube instances.