KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Zoom announced today that it will roll out end-to-end encryption (E2EE) for all users starting next week, as part of a 30-day technical preview.
To start using E2EE when joining new meetings during this roll out phase, meeting participants will have to join using the Zoom desktop client, mobile app, or from Zoom Rooms.
Users will know if their meeting uses E2EE if a green shield logo with a padlock is displayed in the upper left corner of the window.
“We’re excited to announce that starting next week, Zoom’s end-to-end encryption (E2EE) offering will be available as a technical preview, which means we’re proactively soliciting feedback from users for the first 30 days,” Zoom Head of Security Engineering Max Krohn said today.
“Zoom users – free and paid – around the world can host up to 200 participants in an E2EE meeting on Zoom, providing increased privacy and security for your Zoom sessions.”

All E2EE encryption keys are generated by meeting participants’ machines instead of Zoom’s own servers, thus making all exchanged data indecipherable by Zoom or other third parties, with the exception of each meeting participant.
Also Read: Personal Data Websites: 3 Things That You Must Be Informed
“In typical meetings, Zoom’s cloud generates encryption keys and distributes them to meeting participants using Zoom apps as they join,” Krohn explained.
“With Zoom’s E2EE, the meeting’s host generates encryption keys and uses public key cryptography to distribute these keys to the other meeting participants.
“Zoom’s servers become oblivious relays and never see the encryption keys required to decrypt the meeting contents.”
To start using E2EE when joining Zoom meetings, users have to enable E2EE meetings at the account level and opt-in for E2EE meetings on a per-meeting basis.
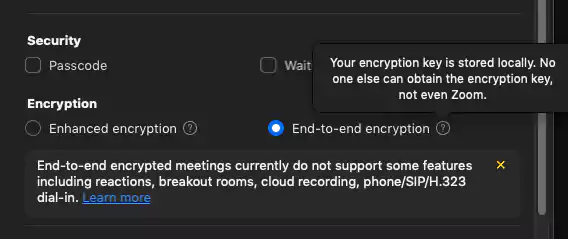
While E2EE provides users with improved security, privacy, and data protection to Zoom meetings, some functionality is limited when it is enabled.
“Enabling this version of Zoom’s E2EE in your meetings disables certain features, including join before host, cloud recording, streaming, live transcription, Breakout Rooms, polling, 1:1 private chat, and meeting reactions,” Krohn added.
An initial draft cryptographic design for Zoom’s E2EE offering was published on GitHub on May 22 and a second updated version was uploaded on June 17 (a list of all the changes can be found here).
Also Read: Trusted Data Sharing Framework IMDA Announced In Singapore
The E2EE meeting option was first announced by Zoom in May 2020 as a feature that will only be available to paying customers, with free/basic users to only get access to 256-bit GCM encryption.
These plans were changed in June when Zoom’s CEO Eric S. Yuan said that free/basic users will also be able to use E2EE after verifying their accounts via additional identification such as their phone number.
“Free/Basic users seeking access to E2EE will participate in a one-time verification process that will prompt the user for additional pieces of information, such as verifying a phone number via text message,” Zoom also confirmed in today’s announcement.
“We are confident that by implementing risk-based authentication, in combination with our current mix of tools — including our work with human rights and children’s safety organizations and our users’ ability to lock down a meeting, report abuse, and a myriad of other features made available as part of our security icon — we can continue to enhance the safety of our users.”
Zoom estimates that the next E2EE rollout phase will start in 2021, adding Single sign-on (SSO) integration and better identity management.