KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The reason for the recent notification from Staples to some of its customers about exposed order details was caused by insufficient protections for retrieving shopper information from current and past orders.
Staples said that they found no evidence of unauthorized purchases on behalf of impacted customers and that they fixed the issue.
The alert lacks any technical details that would explain the nature of the problem, leading to some speculation that it was prompted by a hacker incident.
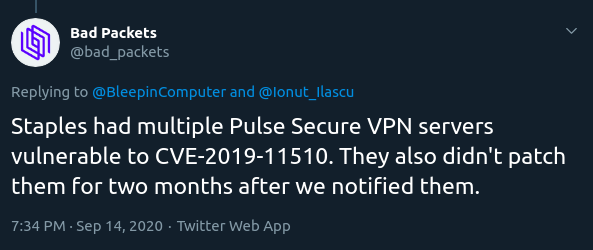
This theory was plausible, especially since threat intelligence company Bad Packets revealed that Staples kept several Pulse Secure VPN servers unpatched for CVE-2019-11510 a long time.
BleepingComputer learned that Staples had two endpoints that allowed customers to track their purchases using the order number and the postal code (ZIP) and one of them could reveal info on someone else’s order.
Also Read: Cost of GDPR Compliance for Singapore Companies
Two factors contributed to this, one being that the order numbers were sequential, so adding or subtracting a number from them would give a valid order ID for a purchase from a different customer.
Another factor was that requesting tracking info of a package did not require a ZIP code, although the field was present.
Starting from a valid order number, a hacker could learn the route of a package (city, state) and, eventually, the delivery address. This significantly reduces the effort of finding out the ZIP code for the final destination.
By combining an order number with the correct delivery ZIP code, a hacker could call another endpoint to get the full order details of a customer.
Letting clients track their purchases using just these two details is common and sufficiently secure, as long as order IDs are not sequential, because the probability to hit a valid combination is very low.
In the case of Staples, a correct pairing exposed the following details:
The same endpoint provided details about current orders, too, which means that someone could cause some trouble by canceling them or initiating a return. With the destination address was exposed, the risk of stealing the goods upon delivery also existed. Furthermore, this information could enable phishing attacks over both email and phone.
From information received by BleepingComputer, not all customers that ordered from Staples recently received the email about their info being exposed.
Staples confirmed to BleepingComputer that the issue no longer exists. We learned that it took the company close to two weeks to solve the problem from the time they were alerted of the risk.
Also Read: How To Make Effective Purchase Order Template Singapore