KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





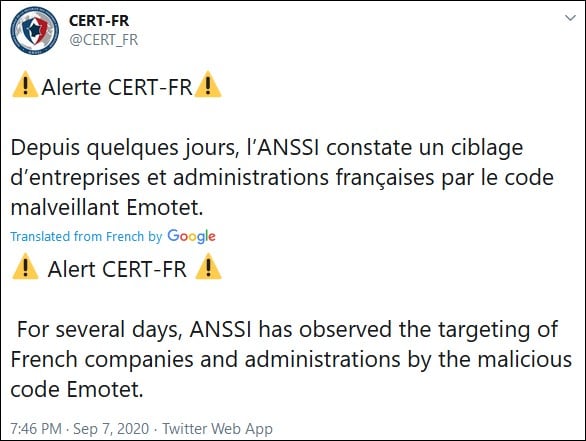
The French national cyber-security agency today published an alert warning of a surge in Emotet attacks targeting the private sector and public administration entities throughout the country.
French public administration has three sub-sectors: central public administrations (APUC), local government (LUFA), and social security administrations (ASSO).
Emotet, originally a run-of-the-mill banking Trojan first spotted in 2014, is now a malware botnet used by a threat group tracked as TA542 and Mummy Spider.
The malware is used by the threat actors to drop other malware families including the Trickbot (a known vector used to deploy Ryuk and Conti ransomware payloads) and the QakBot trojans on infected systems.
“For several days, ANSSI has observed the targeting of French companies and administrations by the Emotet malware,” the ANSSI (Agence Nationale de la Sécurité des Systèmes d’Information) alert bulletin reads.
“Special attention should be paid to this because Emotet is now used to deploy other malicious code that may have a strong impact on the activity of victims.”
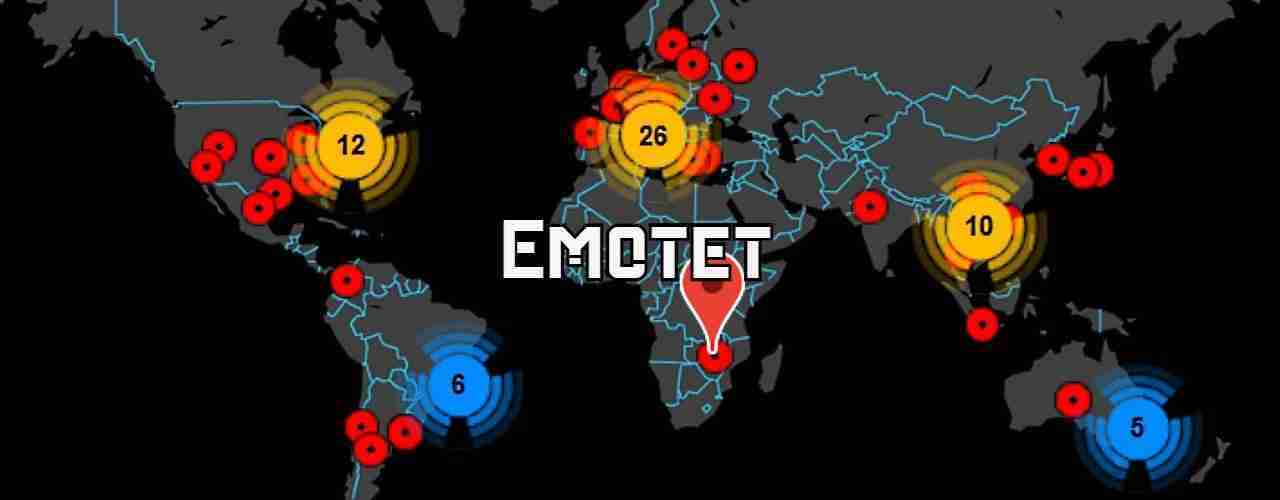
As ANSSI noticed, the botnet is targeting “all types of business sectors around the world,” with attacks against French organizations suddenly increasing in the last few days.
ANNSI also provides a list of recommendations organizations should follow to prevent Emotet infections and to properly react after they systems get compromised:
• Make users aware not to enable macros in attachments and to be particularly attentive to the emails they receive and reduce the execution of macros.
• Limit Internet access for all agents to a controlled white list.
• Disconnect compromised machines from the network without deleting data.
• Generally speaking, removal/cleaning by antivirus is not a sufficient guarantee. Only the reinstallation of the machine ensures the erasure of the implant.
• Send the samples (.doc and .eml) available to you for analysis to ANSSI in order to determine the IoCs that can be shared. This point is essential because the attacker’s infrastructure evolves frequently, access to recent samples is therefore essential.
Also read: Personal Data Websites: 3 Things That You Must Be Informed
This alert comes after the Emotet malware botnet came back to life with a massive campaign of malicious spam — camouflaged as payment reports, invoices, employment opportunities, and shipping information — delivering malicious Word document and spreadsheet attachments starting July 17 via all its server clusters.
As Binary Defense researcher James Quinn told BleepingComputer at the time, Emotet was last seen on Feb 7th, 2020, with the malware going quiet for five months and sending no spam emails until July.
“Since reemerging on July 17, Emotet has sustained its activities with daily spam runs spewing more than 500K emails every day (except weekends) starting at around 2:00 AM Pacific Time (UTC -7),” Microsoft said at the time.
Since it returned back to life, Emotet started installing the TrickBot trojan on infected Windows computers, later switching to fully replace the TrickBot payloads and heavily spreading QakBot malware.
At the moment, reports say that QakBot will deliver ProLock ransomware as final payloads on some of the systems initially compromised by Emotet.
Emotet is now also using stolen attachments to improve the authenticity of its malicious emails, the first time it does so Quinn told BleepingComputer.
This new tactic adds to the leveraging of hijacked email conversation threads where it injects malicious URLs or attachments in new emails attached to existing conversations (as discovered by Minerva Labs in March 2019).
Since it came back online, Emotet has ranked first in a list of top 10 malware strains analyzed on the interactive malware analysis platform Any.Run.
This top puts it head and shoulders above the next malware (the Agent Tesla Remote Access Trojan), with more than then times the number of samples submitted for analysis.
Also read: Computer Misuse Act Singapore: The Truth And Its Offenses