KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A reverse engineer discovered a new zero-day vulnerability in most Windows 10 editions, which allows creating files in restricted areas of the operating system.
Exploiting the flaw is trivial and attackers can use it to further their attack after initial infection of the target host, albeit it works only on machines with Hyper-V feature enabled.
Reverse engineer Jonas Lykkegaard posted last week a tweet showing how an unprivileged user can create an arbitrary file in ‘system32,’ a restricted folder holding vital files for Windows operating system and installed software.
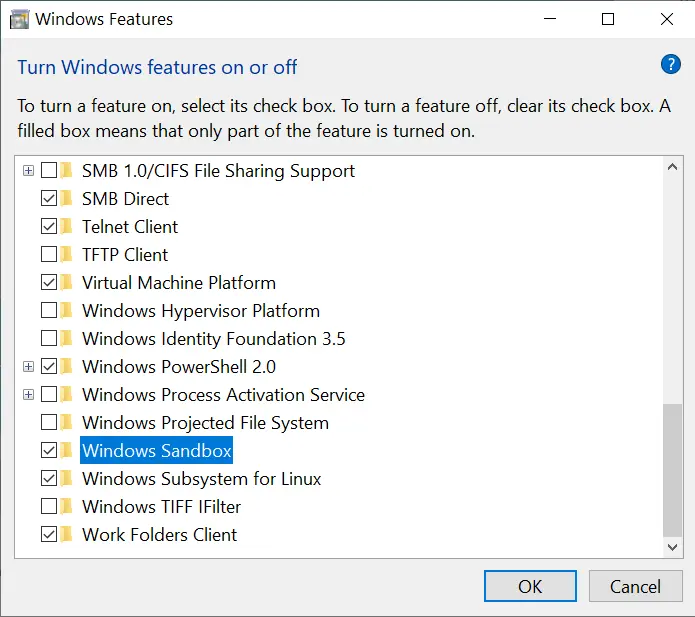
However, this works only if Hyper-V is already active, something that limits the range of targets since the option is disabled by default and is present in Windows 10 Pro, Enterprise, and Education.
Hyper-V is Microsoft’s solution to creating virtual machines (VM) on Windows 10. Depending on the physical resources available on the host, it can run at least three virtual instances.
Given sufficient hardware resources, Hyper-V can run large VMs with 32 processors and 512GB of RAM. An average user user may not have a use for such a virtual machine but they may run Windows Sandbox, an isolated environment for executing programs or loading websites that are not trusted, without risking to infect the normal Windows operating system.
Microsoft introduced Windows Sandbox with the May 2019 Update, in Windows 10 version 1903. Turning on this feature automatically enables Hyper-V.
To demonstrate the vulnerability, Lykkegaard created in \system32 an empty file named phoneinfo.dll. Making any changes in this location requires elevated privileges but these restrictions are irrelevant when Hyper-V is active.
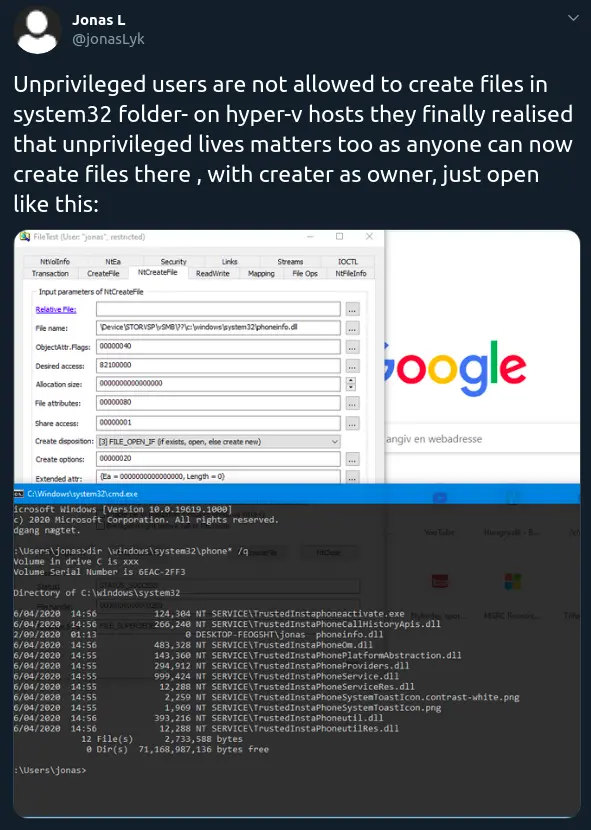
Since the creator of the file is also the owner, an attacker can use this to place malicious code inside that would be execute with elevated privileges when needed.
CERT/CC vulnerability analyst Will Dormann confirmed that the vulnerability exists and that exploiting it requires literally no effort from an attacker on the host.
The researcher told BleepingComputer that the vulnerable component is ‘storvsp.sys’ (Storage VSP – Virtualization Service Provider), a server-side Hyper-V component.
Also read: Website Ownership Laws: Your Rights And What It Protects
Although this vulnerability is easy to exploit there are more dangerous issues in Windows 10 that Microsoft should address. This is one reason he decided to make it public and not report it through Microsoft’s bug bounty program.
Lykkegaard pointed BleepingComputer to a thread with the vulnerabilities he found and told us that one of the worst bugs he reported allowed manipulating UEFI (Unified Extensible Firmware Interface) applications – bootloaders, operating system kernel – that reside as files on the EFI partition.
He says that Microsoft’s recent slash of rewards for high-severity privilege escalation bugs from $20,000 to $2,000 also contributed to sharing the issue publicly since the effort simply is no longer worth it.
“Until now, I have always submitted my findings to MS and waited till they were patched, but with the recent bounty change it is not worth it,” Lykkegaard told us.
However, he would still make the effort to find and report this kind of bugs in Windows, and gladly so, if Microsoft offered him the choice of taking the lower reward or opt for a larger donation from the company to a project that contributed to the education of less fortunate children, such as One Laptop per Child.
Also read: 5 Self Assessment Tools To Find The Right Professional Fit

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
