KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A phishing campaign deployed recently at various businesses uses the company’s home page to disguise the attack and trick potential victims into providing login credentials.
This is a new tactic, researchers say, that loads the legitimate page of the business and applies a fake login box on top of it.
Also read: Website Ownership Laws: Your Rights And What It Protects
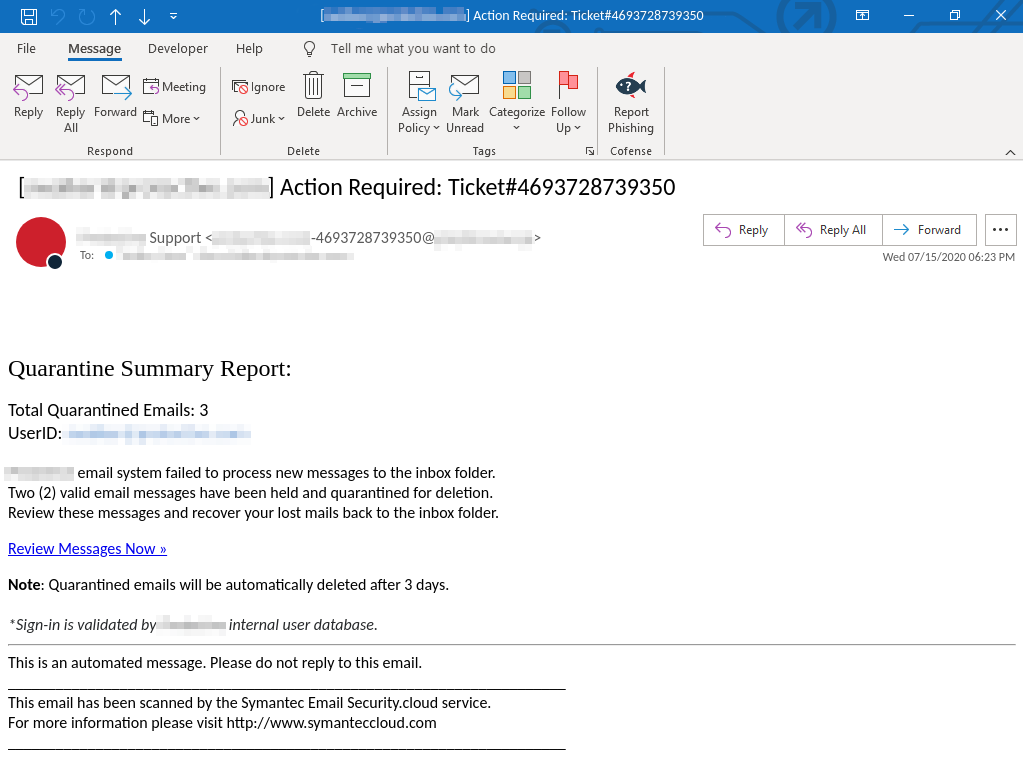
The attack starts with an email purporting to be from the company technical support team informing that some messages were blocked from reaching the inbox because they were quarantined.
To create a sense of urgency, the message from the attacker states that the emails are scheduled for deletion unless the recipient reviews them and takes action to recover them.
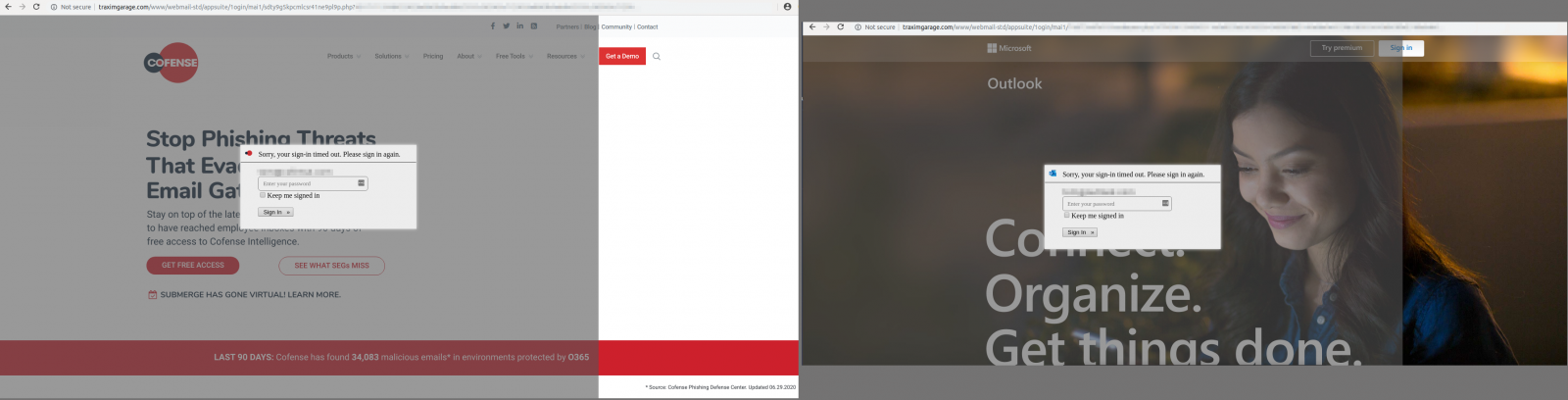
A link in the email body takes the potential victim to the phishing page, where the company’s home page is loaded automatically based on the domain name in the address.
However, the fraudsters added an overlay with a fake login panel, making sure not to cover the entire page. This way, employees suspicious of an attack can click on links and see that they are legitimate.
The overlay method has been used in the past and is now typically seen with banking trojans for Android to steal credentials for online banking and payment card details.
Dylan Main of Cofense says in a blog post today that links for this phishing campaign are from the same domain (‘traximgarage[.]com’) but have specific parameters to load the web page corresponding to the target company.
The fake login overlay has the recipient’s email address typed into the username field, making everything appear more legitimate. Below are two examples showing the tactic in action:
The “quarantined message” theme is not new but Main says that the overlay represents “advanced mechanics to make [the campaign] appear even more legitimate.”
While this method may not be successful in smaller companies, it may prove efficient in larger environments where employees are likely to rely more on email protection systems and be less vigilant.
Also read: 5 Self Assessment Tools To Find The Right Professional Fit