KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





.jpg)
NVIDIA has addressed a vulnerability in the Windows NVIDIA GeForce Experience (GFE) software that could allow local attackers to execute arbitrary code, trigger a denial of service (DoS) state, or access privileged information on unpatched systems.
Even though the security flaw tracked as CVE‑2020‑5964 requires attackers to have local user access to the device and cannot be exploited remotely, it can still be abused with the help of malicious tools delivered to systems running vulnerable NVIDIA GFE versions.
NVIDIA GeForce Experience is the companion software for GeForce GTX, RTX, TITAN X, and other NVIDIA GeForce graphics cards, and it can be installed on computers running Windows 7 or later.
It “keeps your drivers up to date, automatically optimizes your game settings, and gives you the easiest way to share your greatest gaming moments with friends” according to NVIDIA,
Also read: 4 easy guides to data breach assessment
After successfully exploiting the CVE‑2020‑5964 flaw could enable attackers could execute arbitrary code on Windows machines running unpatched NVIDIA GFE software versions.
They could also gain access to sensitive information beyond the permissions initially granted by the compromised system or render them unusable by triggering a denial of service state.
The CVE‑2020‑5964 vulnerability fixed as part of the July 2020 security update is detailed below, together with a full description and the CVSS V3 base score assigned by NVIDIA.
| CVE ID | Description | Base Score | Vector |
| CVE‑2020‑5964 | NVIDIA GeForce Experience software contains a vulnerability in the service host component, in which the integrity check of application resources may be missed. Such an attack may lead to code execution, denial of service, or information disclosure. | 6.5 | AV:L/AC:L/PR:H/UI:R/S:U/C:H/I:H/A:H |
NVIDIA says that the “risk assessment is based on an average of risk across a diverse set of installed systems and may not represent the true risk of your local installation.
The company also advises “consulting a security or IT professional to evaluate the risk to your specific configuration.”
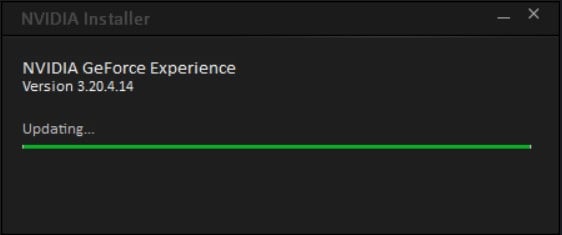
The security issue impacts Windows computers running versions of NVIDIA GeForce Experience before 3.20.4.
“Earlier software branch releases that support this product are also affected,” NVIDIA also explained. “If you are using an earlier branch release, upgrade to the latest branch release.”
To apply the security update, NVIDIA GeForce Experience users can download the latest software version from the GeForce Experience Downloads page or launch the GFE client on their Windows computers to have it applied using the built-in automatic update mechanism.
Also read: Privacy policy template important tips for your business