KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







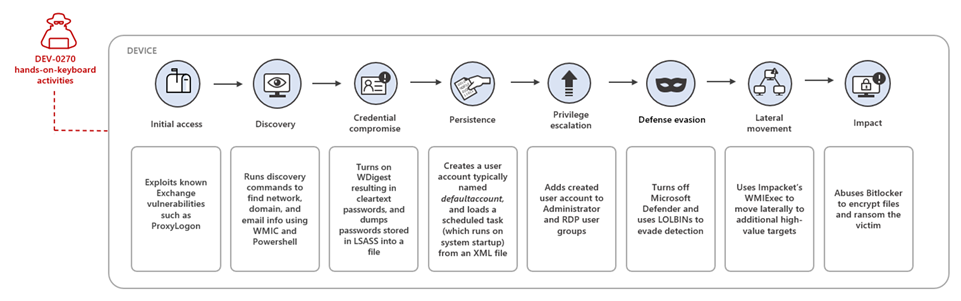
Microsoft says an Iranian state-sponsored threat group it tracks as DEV-0270 (aka Nemesis Kitten) has been abusing the BitLocker Windows feature in attacks to encrypt victims’ systems.
Redmond’s threat intelligence teams found that the group is quick to exploit newly disclosed security vulnerabilities and extensively uses living-off-the-land binaries (LOLBINs) in attacks.
This aligns with Microsoft’s findings that DEV-0270 uses BitLocker, a data protection feature that provides full volume encryption on devices running Windows 10, Windows 11, or Windows Server 2016 and above.
Also Read: Personal Data Websites: 3 Things That You Must Be Informed
“DEV-0270 has been seen using setup.bat commands to enable BitLocker encryption, which leads to the hosts becoming inoperable,” the Microsoft Security Threat Intelligence explained.
“For workstations, the group uses DiskCryptor, an open-source full disk encryption system for Windows that allows for the encryption of a device’s entire hard drive.”
The time to ransom (TTR) between the initial access and the ransom note being deployed on locked systems was around two days, and DEV-0270 has been observed demanding victims to pay $8,000 for decryption keys following successful attacks.
Redmond says this is a sub-group of the Iranian-backed Phosphorus cyber-espionage group (aka Charming Kitten and APT35) known for targeting and collecting intelligence from high-profile victims linked to governments, NGOs, and defense organizations worldwide.
DEV-0270 appears to be moonlighting “for personal or company-specific revenue generation,” according to a low confidence assessment from Microsoft.
Also Read: PDPA For Companies: Compliance Guide For Singapore Business
Based on “numerous infrastructure overlaps,” Microsoft says the group is being operated by an Iranian company known under two aliases: Secnerd (secnerd[.]ir) and Lifeweb (lifeweb[.]it).
“These organizations are also linked to Najee Technology Hooshmand (ناجی تکنولوژی هوشمند), located in Karaj, Iran,” Redmond added.
“The group is typically opportunistic in its targeting: the actor scans the internet to find vulnerable servers and devices, making organizations with vulnerable and discoverable servers and devices susceptible to these attacks.”
Since many of DEV-0270’s attacks have exploited known vulnerabilities in Exchange (ProxyLogon) or Fortinet (CVE-2018-13379), companies are advised to patch their Internet-facing servers to block exploitation attempts and subsequent ransomware attacks.
Similar malicious activity linked to a threat group Secureworks tracks as COBALT MIRAGE (with elements overlapping the Phosphorus APT group) was reported by SecureWorks’ Counter Threat Unit (CTU) in May.