KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







For more than a year, North Korean hackers have been running a ransomware operation called HolyGhost, attacking small businesses in various countries.
The group has been active for quite a while but it failed to gain the notoriety and financial success of other gangs even if the operation followed the same recipe: double extortion combined with a leak site to publish the name of the victims and stolen data.
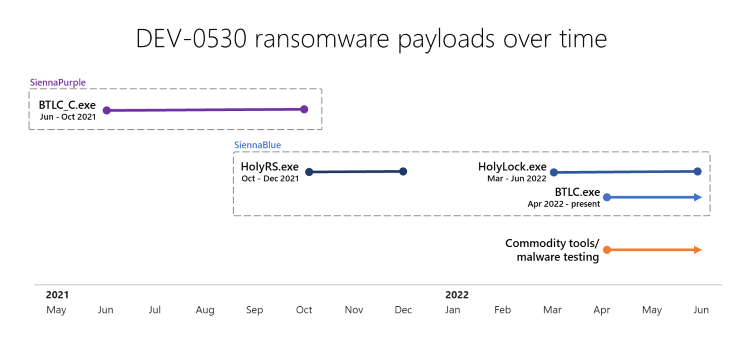
Researchers at Microsoft Threat Intelligence Center (MSTIC) are tracking the Holy Ghost ransomware gang as DEV-0530. In a report earlier today, they say that the first payload from this threat actor was seen last year in June.
Classified as SiennaPurple (BTLC_C.exe), the early Holy Ghost ransomware variant did not come with many features compared to the subsequent Go-based versions that emerged in October 2021.
Microsoft tracks the newer variants as SiennaBlue (HolyRS.exe, HolyLocker.exe, and BTLC.exe) and notes that their functionality expanded over time to include multiple encryption options, string obfuscation, public key management, and internet/intranet support.
Also Read: PDPA compliance for the healthcare sector
The researchers say that DEV-0530 managed to compromise several targets, mainly small-to-midsize businesses. Among victims were banks, schools, manufacturing organizations, and event and meeting planning companies.
“The victimology indicates that these victims are most likely targets of opportunity. MSTIC suspects that DEV-0530 might have exploited vulnerabilities such as CVE-2022-26352 (DotCMS remote code execution vulnerability) on public-facing web applications and content management systems to gain initial access into target networks” – Microsoft Threat Intelligence Center
Holy Ghost actors followed the pattern of a typical ransomware attack and stole data before deploying the encryption routine on infected systems.
The attacker left a ransom note on the compromised machine and they also emailed the victim with a link to a sample of stolen data to announce that they were willing to negotiate a ransom in exchange for the decryption key.
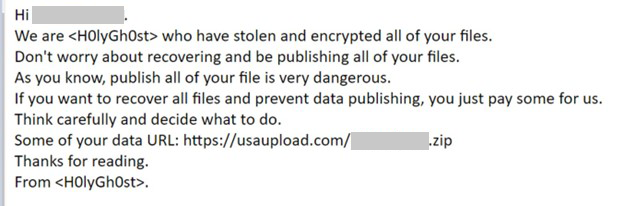
Usually, the actors demanded a small payout between 1.2 to 5 bitcoins, or up to about $100,000 at the current exchange rate.
Even if the demands were not large, the attacker was willing to negotiate and sometimes lowered the price to less than a third of the initial demand, MSTIC says.
Also Read: The difference between data privacy and data protection
This detail, the infrequent rate of attacks, and the random selection of victims add to the theory that the Holy Ghost ransomware operation may not be controlled by the North Korean government.
Instead, hackers working for the Pyongyang regime may be doing this on their own, for personal financial gain.
The connection with state-backed hacker groups is present, though, as MSTIC found communication between email accounts belonging to Holy Ghost and the Andariel, a threat actor part of the Lazarus Group under North Korea’s Reconnaissance General Bureau.
The link between the two groups is made stronger by the fact that both were “operating from the same infrastructure set, and even using custom malware controllers with similar names,” the researchers say.
Holy Ghost’s website is down at the moment but the attacker used the little visibility it had to pose as a legitimate entity trying to help victims improve their security posture.
Furthermore, they motivate their actions as an effort to “close the gap between the rich and poor” and to “help the poor and starving people.”
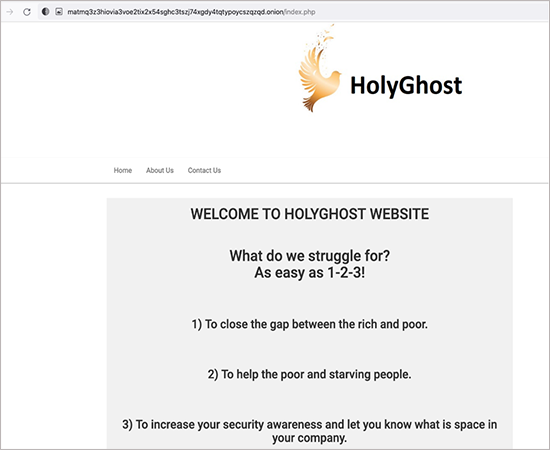
Like other actors in the ransomware business, Holy Ghost assures victims that they would not sell or leak the stolen data if they get paid.
Microsoft’s report includes a set of recommended actions to prevent infections with Holy Ghost payloads as well as some indicators of compromise discovered while investigating the malware.
Holy Ghost is the second ransomware operation connected to North Korea.
Last week, a joint advisory from the FBI, CISA, and the U.S. Treasury Department warned about Maui ransomware targeting healthcare organizations with the support of North Korean government.