KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





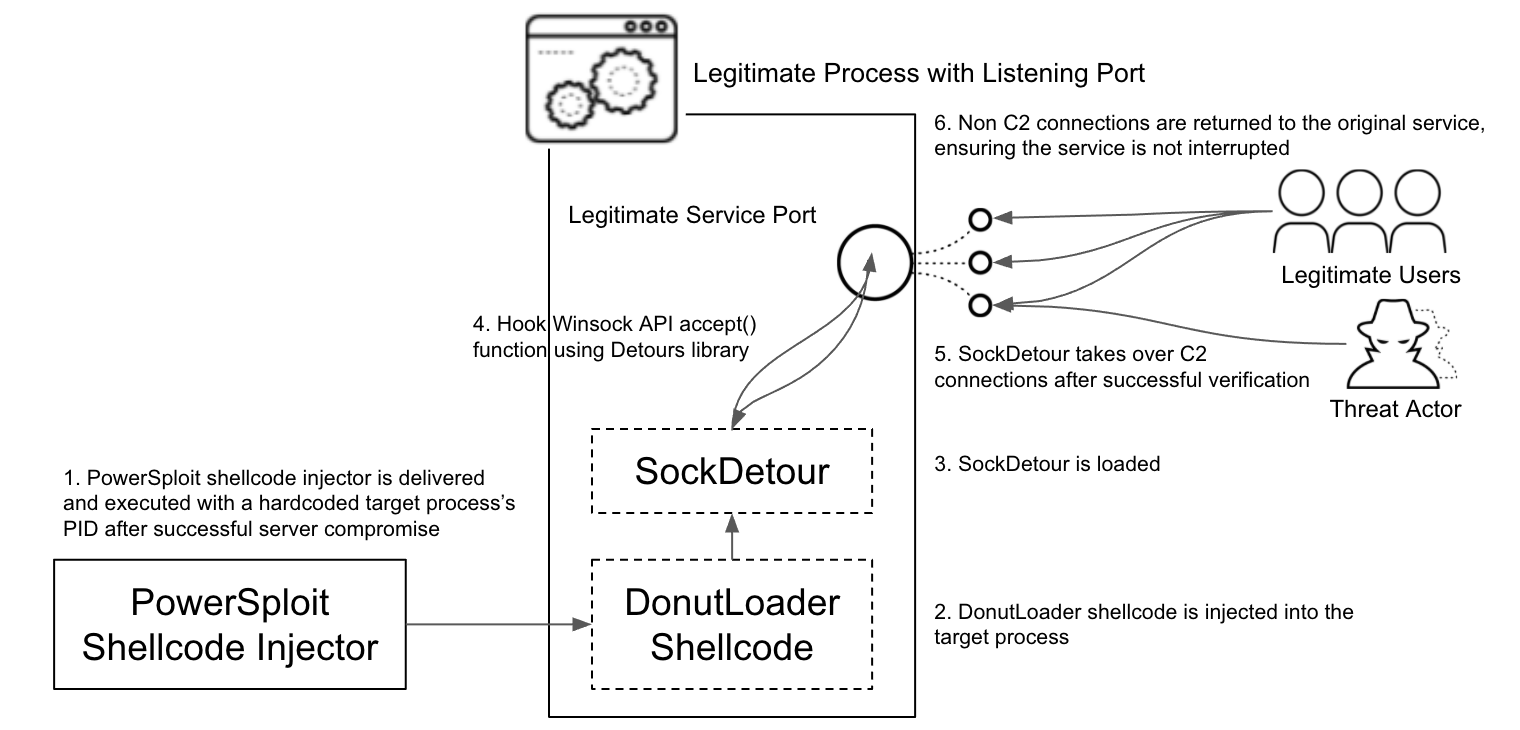
A new custom malware dubbed SockDetour found on systems belonging to US defense contractors has been used as a backup backdoor to maintain access to compromised networks.
The malicious payload was spotted by Unit 42 security researchers, who believe that its operators kept the backdoor under the radar for a long time as it has been used in the wild since at least July 2019.
SockDetour’s stealthiness can be explained by the fact that it “operates filelessly and socketlessly” on infected Windows servers by hijacking network connections, making it a lot harder to detect at the host and network levels.
The connection hijacking is done using the legitimate Microsoft Detours library package used for Windows API call monitoring and instrumentation.
Also Read: 7 Client Data Protection Tips to Keep Customers Safe
“With such implementation, SockDetour [..] serves as a backup backdoor in case the primary backdoor is detected and removed by defenders,” Unit 42 explained.
Also Read: 9 Policies For Security Procedures Examples
In one of the attacks, the threat actors also used a very specific delivery server, a QNAP network-attached storage (NAS) device typically used by small businesses and previously infected with QLocker ransomware — they likely exploited the same security flaw (the CVE-2021-28799 remote code execution bug) to gain access to the server.
The researchers first spotted the malware being deployed onto the Windows server of at least one US defense contractor on July 27, 2021, which led to the discovery of three other defense orgs being targeted by the same group with the same backdoor.
“Based on Unit 42’s telemetry data and the analysis of the collected samples, we believe the threat actor behind SockDetour has been focused on targeting U.S.-based defense contractors using the tools,” the researchers revealed.
“Unit 42 has evidence of at least four defense contractors being targeted by this campaign, with a compromise of at least one contractor.”
The SockDetour backdoor is used in attacks by an APT activity cluster tracked by Unit 42 as TiltedTemple and previously linked to attacks exploiting several vulnerabilities in Zoho products, including ManageEngine ADSelfService Plus (CVE-2021-40539) and ServiceDesk Plus (CVE-2021-44077).