KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






North Korean-backed hacking group Lazarus has added the Windows Update client to its list of living-off-the-land binaries (LoLBins) and is now actively using it to execute malicious code on Windows systems.
The new malware deployment method was discovered by the Malwarebytes Threat Intelligence team while analyzing a January spearphishing campaign impersonating the American security and aerospace company Lockheed Martin.
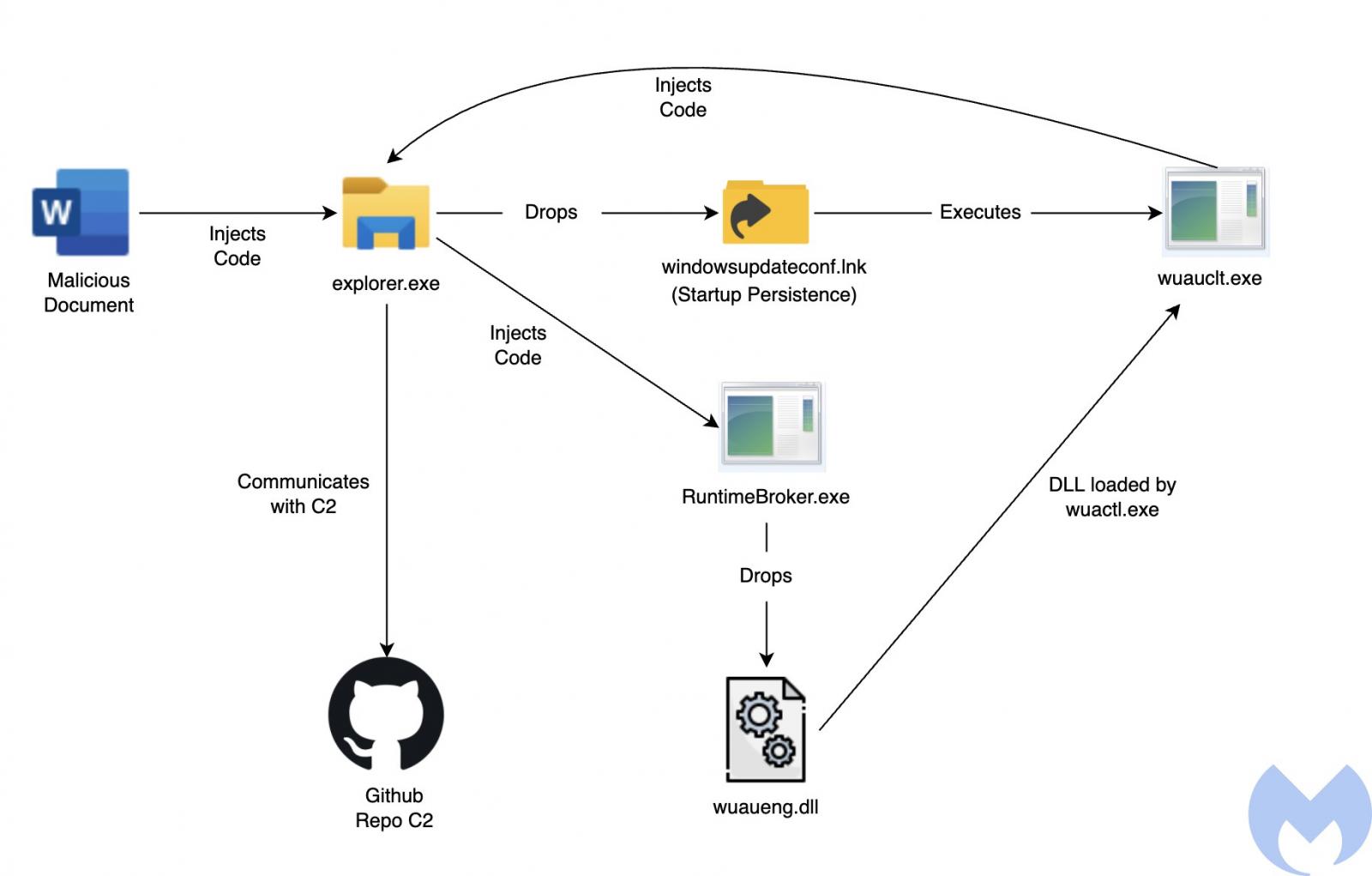
After the victims open the malicious attachments and enable macro execution, an embedded macro drops a WindowsUpdateConf.lnk file in the startup folder and a DLL file (wuaueng.dll) in a hidden Windows/System32 folder.
In the next stage, the LNK file is used to launch the WSUS / Windows Update client (wuauclt.exe) to execute a command that loads the attackers’ malicious DLL.
Also Read: How To Make A PDPC Complaint: With Its Importance And Impact
“This is an interesting technique used by Lazarus to run its malicious DLL using the Windows Update Client to bypass security detection mechanisms,” Malwarebytes said.
The researchers linked these attacks to Lazarus based on several pieces of evidence, including infrastructure overlaps, document metadata, and targeting similar to previous campaigns.
As BleepingComputer reported in October 2020, this tactic was discovered MDSec researcher David Middlehurst, who found that attackers could use the Windows Update client to execute malicious code on Windows 10 systems (he also spotted a sample using it in the wild).
This can be done by loading an arbitrary specially crafted DLL using the following command-line options (the command Lazarus used to load their malicious payload):
wuauclt.exe /UpdateDeploymentProvider [path_to_dll] /RunHandlerComServerMITRE ATT&CK classifies this type of defense evasion strategy as Signed Binary Proxy Execution, and it allows attackers to bypass security software, application control, and digital certificate validation protection.
In this case, threat actors do it by executing malicious code from a previously dropped malicious DLL, loaded using the Windows Update client’s Microsoft-signed binary.
The Lazarus Group (also tracked as HIDDEN COBRA by US intel agencies) is a North Korean military hacking group active for more than a decade, since at least 2009.
Also Read: Basic Info On How Long To Keep Accounting Records In Singapore?
Its operators coordinated the 2017 global WannaCry ransomware campaign and have been behind attacks against high-profile companies such as Sony Films and multiple banks worldwide.
Last year, Google spotted Lazarus targeting security researchers in January as part of complex social engineering attacks and a similar campaign during March.
They were also observed using the previously undocumented ThreatNeedle backdoor in a large-scale cyber-espionage campaign against the defense industry of more than a dozen countries.
US Treasury sanctioned three DPRK-sponsored hacking groups (Lazarus, Bluenoroff, and Andariel) in September 2019, and the US government offers a reward of up to $5 million for info on Lazarus activity.