KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft Defender for Endpoint is currently showing “sensor tampering” alerts linked to the company’s newly deployed Microsoft 365 Defender scanner for Log4j processes.
The alerts are reportedly mainly shown on Windows Server 2016 systems and warn of “possible sensor tampering in memory was detected by Microsoft Defender for Endpoint” created by an OpenHandleCollector.exe process.
Admins have been dealing with this issue since at least December 23, according to customer reports.
Also Read: The 3 Main Benefits Of PDPA For Your Business
While this Defender process’ behavior is tagged as malicious, there’s nothing to worry about since these are false positives, as revealed by Tomer Teller, Principal Group PM Manager at Microsoft, Enterprise Security Posture.
Microsoft is currently looking into this Microsoft 365 Defender issue and working on a fix that the company should soon deliver to affected systems.
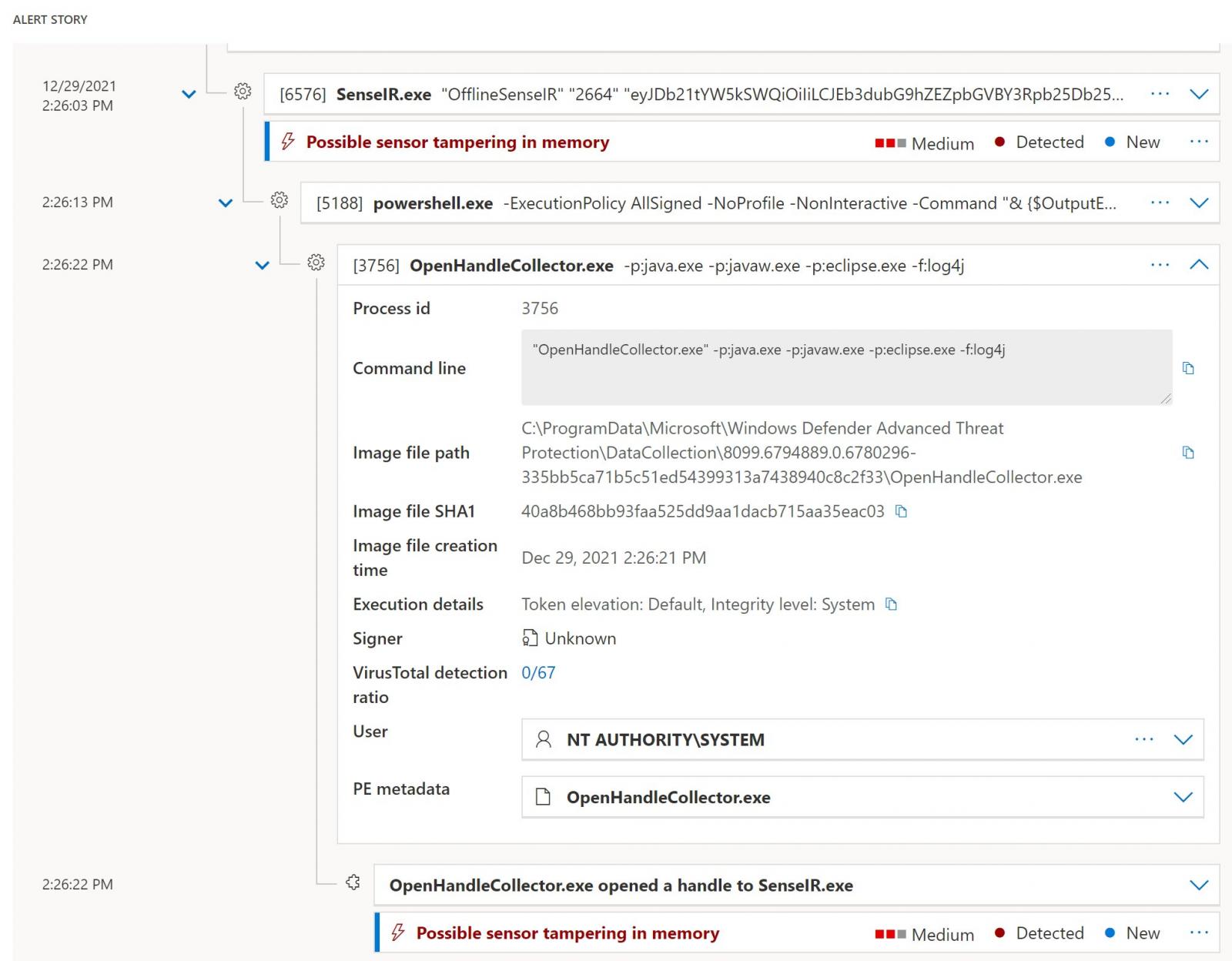
“This is part of the work we did to detect Log4J instances on disk. The team is analyzing why it triggers the alert (it shouldn’t of course),” Teller explained.
As Microsoft shared on Tuesday, this newly deployed Log4j scanner was rolled out with a new consolidated Microsoft 365 Defender portal Log4j dashboard for threat and vulnerability management.
Also Read: What Do 4 Messaging Apps Get From You? Read The iOS Privacy App Labels
The new dashboard is designed to help customers identify and remediate files, software, and devices exposed to attacks exploiting Log4j vulnerabilities.
Since October 2020, Windows admins had to deal with other Defender for Endpoint, including one that marked Office documents as Emotet malware payloads, one that showed network devices infected with Cobalt Strike, and another that tagged Chrome updates as PHP backdoors.
This is a developing story …