KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






A malware developer unleashed their creation on their system to try out new features and the data ended up on a cybercrime intelligence platform, exposing a glimpse of the cybercriminal endeavor.
The threat actor is the developer of Raccoon, an information stealer that can collect data from dozens of applications and has been growing in popularity for the past two years.
While testing a variant of the stealer, the developer of Raccoon infected their own system, a move that immediately triggered the data to flow to the command and control (C2) server and further on, to cybercrime forums.
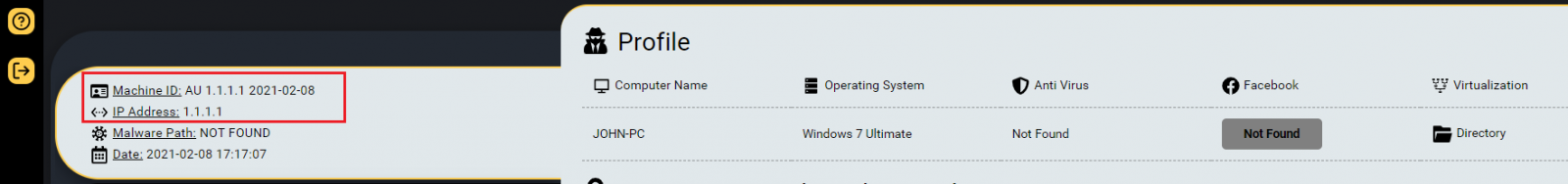
Raccoon developer’s infected test system was found through Hudson Rock’s Cavalier platform, a cybercrime intelligence database that monitors compromised machines.
Alon Gal, Hudson Rock co-founder and Chief Technology Officer, says that Raccoon infostealer has more than one million compromised systems that are being tracked through Cavalier.
The researcher told BleepingComputer that the developer of Raccoon infostealer infected their machine in February but went unnoticed because it presented no interest since it was not a machine belonging to the company’s clients.
It attracted attention through its IP address, 1.1.1.1, modified on purpose in the command and control server so that the real one would not get captured, Gal says. Funny enough, the IP address is used by Cloudflare’s public Domain Name System (DNS) resolver.
Also Read: The Top 4W’s of Ethical Hacking
The data collected from the self-infected system shows that the developer tested the malware’s ability to extract passwords from Google Chrome, an essential attribute for any information stealer.
Additional information trawled from the Raccoon test computer revealed a name and multiple email addresses associated with the malware.
Unfortunately, the details are insufficient to determine the identity of Raccoon’s developer. Gal says that the malware creator “likely infected [the machine] on purpose” and was careful enough to remove the details that could reveal who they are before unleashing the malware.
For instance, email addresses used for various services contain either “raccoon” or “raccoonstealer,” indicating that they are used for customer communication.
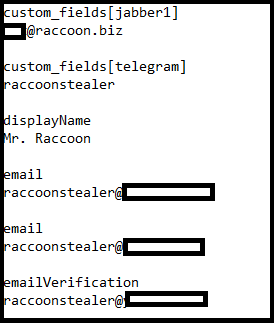
The researcher also found the name Benjamin Engel, a hacker from Berlin and main character in the 2014 German hacker movie “Who Am I.”
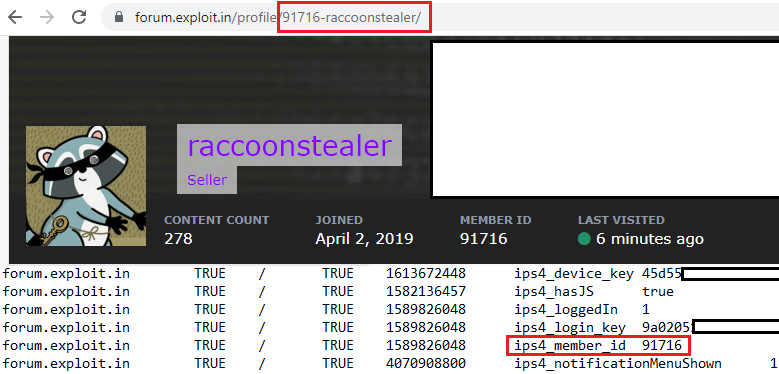
Other details picked from the test system showed that the developer’s test box had cookies indicating logging into a Russian-speaking forum that is popular with prominent cybercriminal groups.
Gal was able to compare the ID in the cookie generated when logging into the forum with the ID attached to the Raccoon stealer account in the community.
Also Read: What is Social Engineering and How Does it Work?
While the information collected this way does not contain the hints necessary to put a real name to Raccoon’s developer, it shows that cybercriminals can also slip up and there is still hope to catch them off guard.