KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Attackers can use a newly disclosed domain name server (DNS) vulnerability publicly known as TsuNAME as an amplification vector in large-scale reflection-based distributed denial of service (DDoS) attacks targeting authoritative DNS servers.
In simpler terms, authoritative DNS servers translate web domains to IP addresses and pass this info to recursive DNS servers that get queried by regular users’ web browsers when trying to connect to a specific website.
Authoritative DNS servers are commonly managed by both government and private organizations, including Internet Service Providers (ISPs) and worldwide tech giants.
Attackers attempting to exploit the TsuNAME DNS vulnerability target vulnerable recursive resolvers and cause them to overwhelm authoritative servers with large amounts of malicious DNS queries.
“Resolvers vulnerable to TsuNAME will send non-stop queries to authoritative servers that have cyclic dependent records,” the researchers explain in their security advisory. [PDF]
“While one resolver is unlikely to overwhelm an authoritative server, the aggregated effect from many looping, vulnerable recursive resolvers may as well do.”
Also Read: What You Should Know About The Data Protection Obligation Singapore
A possible impact following such an attack can be the takedown of directly impacted authoritative DNS servers, potentially causing countrywide Internet outages if a country code top-level domain (ccTLD) is affected.
“What makes TsuNAME particularly dangerous is that it can be exploited to carry out DDoS attacks against critical DNS infrastructure like large TLDs or ccTLDs, potentially affecting country-specific services,” a research paper [PDF] published after disclosure explains.
According to the researchers, popular DNS resolvers such as Unbound, BIND, and KnotDNS are not affected by the TsuNAME DNS bug.
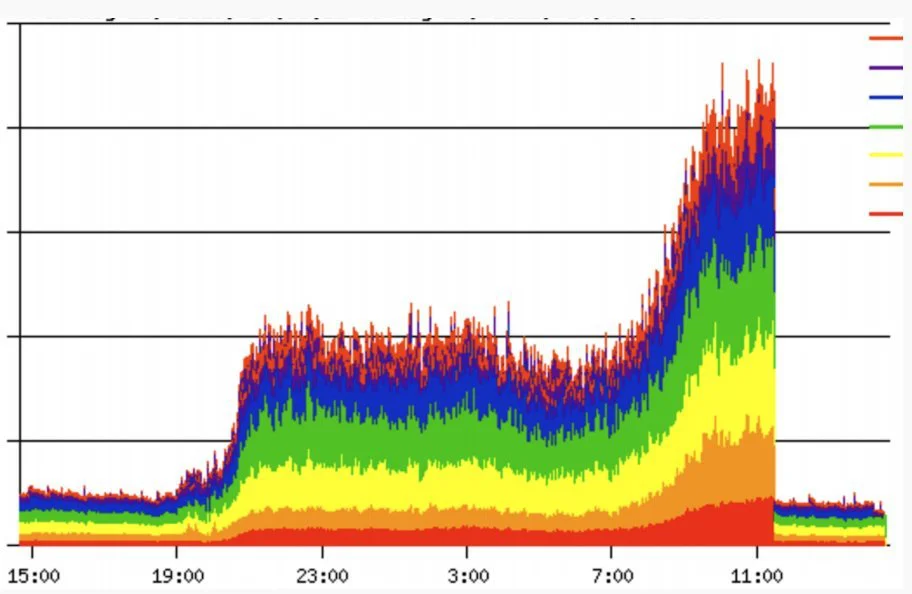
“We observed 50% traffic increases due to TsuNAME in production in .nz traffic, which was due to a configuration error and not a real attack,” the researchers added.
Reports also mention TsuNAME events affecting an EU-based ccTLD that increased the incoming DNS traffic by a factor of 10 due to just two domains with a cyclic dependency misconfiguration.
However, attackers with access to multiple domains and a botnet can do a lot more damage if they misconfigure their domains and start probing open resolvers.
Fortunately, TsuNAME mitigations are available, and they require changes to recursive resolver software “by including loop detection codes and caching cyclic dependent records.”
Authoritative server operators can also reduce the impact of TsuNAME attacks using the open-source CycleHunter tool, which helps prevent such events by detecting and pre-emptively fixing cyclic dependencies in their DNS zones.
Also Read: The Difference Between GDPR And PDPA Under 10 Key Issues
The researchers have already used CycleHunter to examine around 184 million domains in seven TLDs, which allowed them to detect 44 cyclic dependent NS records (mots likely caused by misconfigurations) on roughly 1,400 domain names that could be abused in attacks.