KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Google Alerts continues to be a hotbed of scams and malware that threat actors are increasingly abusing to promote malicious websites.
While Google Alerts has been abused for a long time, BleepingComputer has noticed a significant increase in activity over the past couple of weeks.
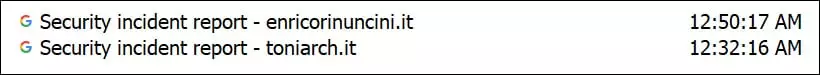
For example, I use Google Alerts to monitor for various terms related to cyberattacks, security incidents, malware, etc. In one particular Google Alert, almost every new article shared with me today by the service led to a scam or malicious website, with two of them shown below.
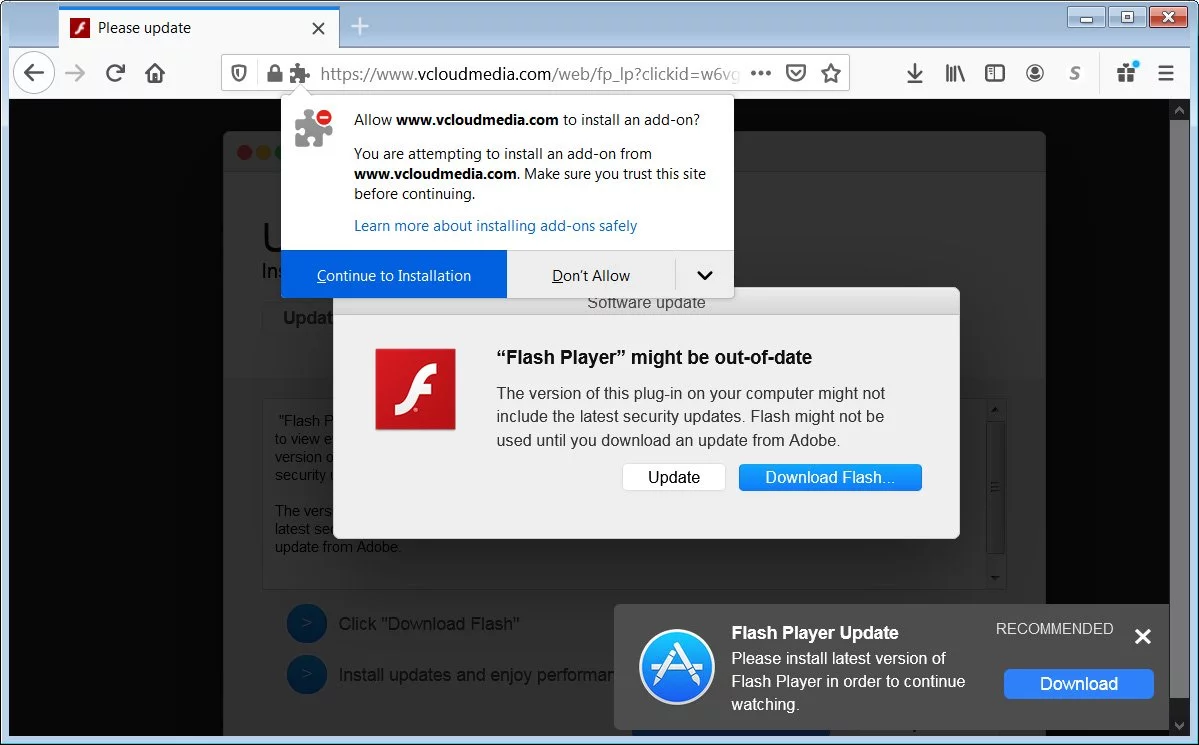
When you open these alerts, instead of being brought to a legitimate web page, you are redirected through a series of sites until you land on one promoting malware, fake adult sites, fake dating apps, adult games, giveaway and sweepstake scams, and unwanted browser extensions.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
Unfortunately, even if you configure your Google Alert only to show you the best results, the scam alerts will often sneak through only to be detected when you open them.
To deceive Google into thinking they are legitimate sites rather than scams, threat actors use a black hat search engine optimization (SEO) technique called ‘cloaking.’
Cloaking is when a website displays different content to visitors than it does search engine spiders.
This cloaking allows the website to look like a plain text or a typical blog post when Google’s search engine spiders visit the page but perform malicious redirects when a user visits the site from a Google redirect.
For example, if you or the GoogleBot spider visits the webpage directly, the site will display a wall of text with high keyword density for the terms they are trying to rank. From the text below, you can see that the threat actor uses a lot of cybersecurity keywords to target well in that category.
However, when a user gets to the site through a Google Alert URL, they will be redirected to malicious sites pushing malware or scams.
For example, when opening up one of the Google Alerts links in Firefox, the link redirected me to a page promoting software called ‘YoutubeToMP3,’ which has 24/69 VirusTotal detections.
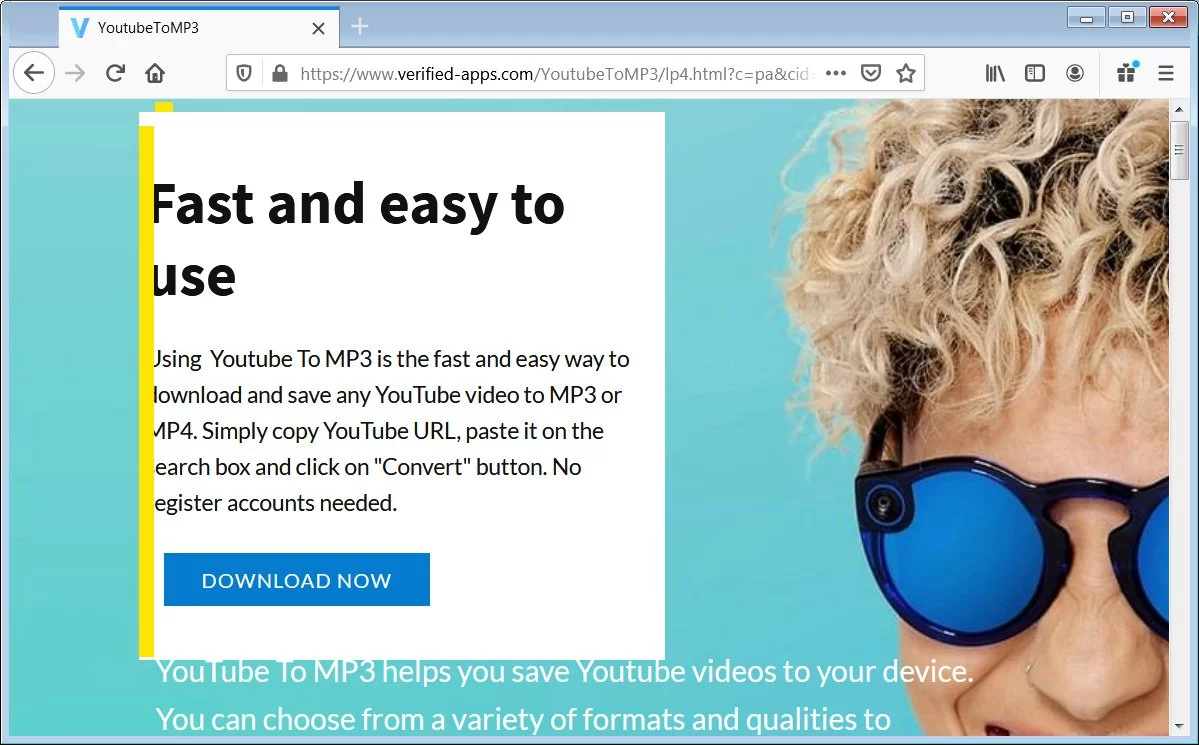
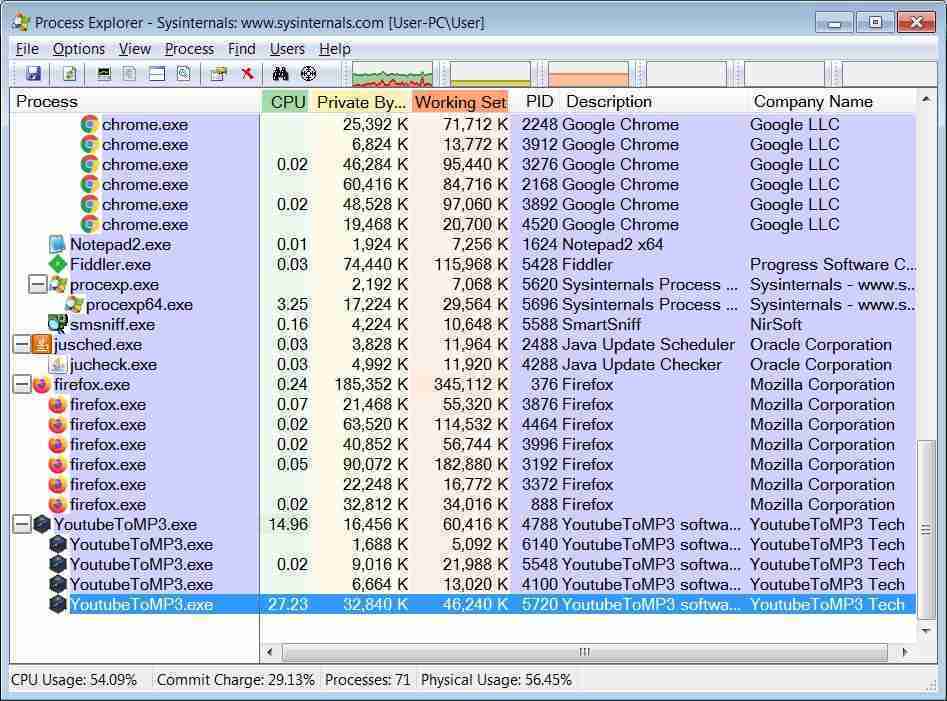
After installing the malware, a headless Chromium browser is launched in the background performing suspicious activity while utilizing 27% of the CPU.
As Google is never shown the redirect to malicious sites, the web page is added to the search index, and a Google Alert is fired off to anyone who is monitoring those keywords.
Also Read: What You Should Know About The Data Protection Obligation Singapore
Those who receive the alert will never know the URL is malicious until they visit the site or their installed antivirus blocks the URL.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
