KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A recent phishing campaign used a clever trick to deliver the fraudulent web page that collects Microsoft Office 365 credentials by building it from chunks of HTML code stored locally and remotely.
The method consists of gluing together multiple pieces of HTML hidden in JavaScript files to obtain the fake login interface and prompt the potential victim to type in the sensitive information.
Victims received an email with just an attachment claiming to be an Excel file (.XLSX) about an investment. In reality, the file is an HTML document with a chunk of URL Encoded text.
Researchers at Trustwave decoded the text and found more decoding ahead as it was further obfuscated through Entity codes. Using GCHQ’s CyberChef, they revealed links to two JavaScript files hosted at “yourjavascript.com,” a domain used for other phishing campaigns.
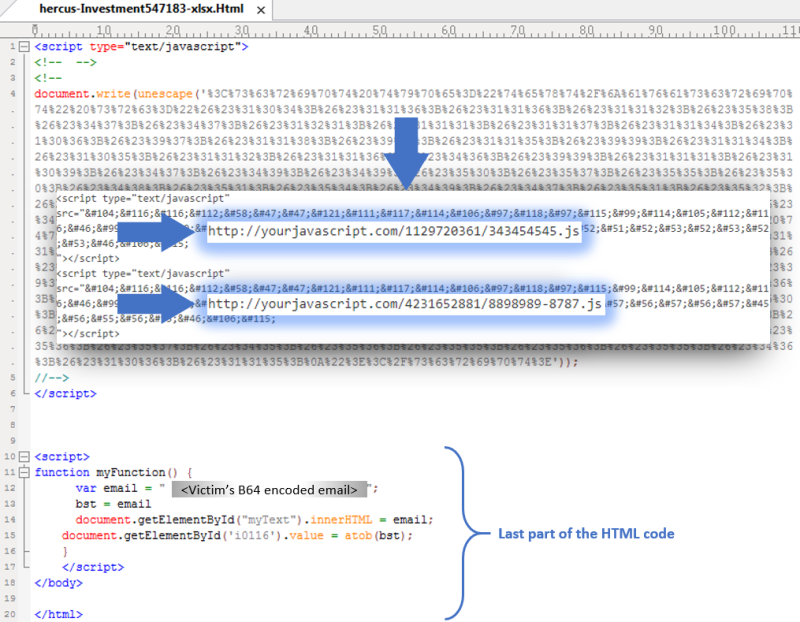
Each of the two JavaScript files had two blocks of encoded text hiding HTML code, URL and Base64 encoded.
Also Read: How To Comply With PDPA: A Checklist For Businesses
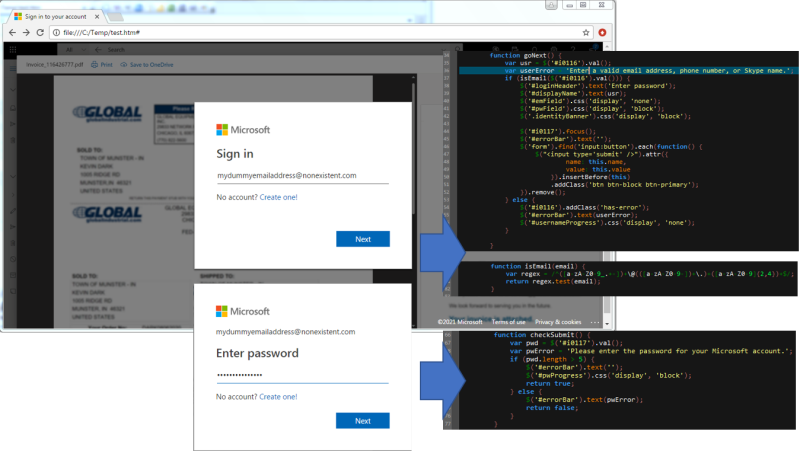
In one of them, the researchers found the beginning of the phishing page and code that validates the email and password from the victim.
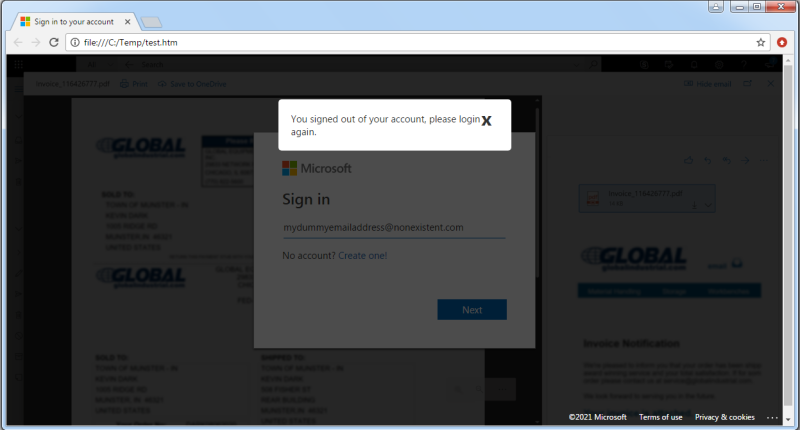
The second JavaScript contained the ‘submit’ function, located via the ‘form’ tags and code that triggered a popup message informing victims that they had been logged out and needed to authenticate again.
In all, the researchers decoded more than 367 lines of HTML code spread in five chunks among the two JavaScript files and one the email attachment, which, stacked together, built the Microsoft Office 365 phishing page.
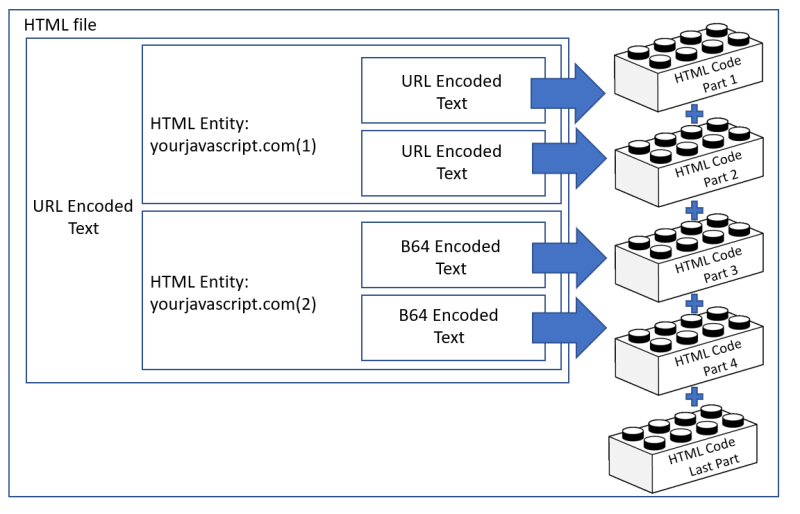
Trustwave said that the unusual thing about this campaign is that the JavaScript is downloaded in obfuscated chunks from a remote location and then pieced together locally.
“This helps the attackers bypass security protections like Secure Email Gateways that might identify the malicious JavaScript from the initial attachment and block it,” the researchers added.
The victim email address is automatically filled in to give a sense of legitimacy. The phishing scams also check to make sure the password is not blank and will use regular expressions to confirm a valid email address.
In a blog post today, Trustwave notes that the URL receiving the stolen credentials for this campaign is still active.
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
The researchers say that the tricks in this campaign are uncommon. Using an HTML attachment pointing to JavaScript code in a remote location and unique encoding, the cybercriminals are looking to avoid detection.