KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A threat actor has infected an e-commerce store with a custom credit card skimmer designed to siphon data stolen by a previously deployed Magento card stealer.
Credit card skimmers (aka payment card skimmers or Magecart scripts) are JavaScript scripts that cybercrime groups known as Magecart groups inject into hacked e-commerce sites as part of web skimming (also known as e-skimming) attacks.
Their end goal is to steal the payment and personal info submitted by the hacked stores’ customers and collect it on remote servers under their control.
Malwarebytes’ security researchers discovered the piggybacking skimmer while investigating a massive wave of compromised online stores running out of support Magento 1 installations.
Also Read: Data Centre Regulations Singapore: Does It Help To Progress?
Even though spotting multiple card skimmer scripts on the same online shop is not unheard of, this one stood out due to its highly specialized nature.
“The threat actors devised a version of their script that is aware of sites already injected with a Magento 1 skimmer,” Malwarebytes’ Head of Threat Intelligence Jérôme Segura explains in a report shared in advance with Bleeping Computer.
“That second skimmer will simply harvest credit card details from the already existing fake form injected by the previous attackers.”
And the threat actors’ efforts to get their hands on the online store’s customer financial info did not stop there: they also deployed a second version of their skimmer designed to inject payment form fields that closely mimic the shop’s legitimate payment processor.
Costway, the retailer affected in this attack, used Magento 1 software on its France, UK, Germany, and Spain online shops, which got compromised around the same date as spotted by Malwarebytes’ crawlers.
The skimmer deployed by the first threat actor who hacked Costway’s sites injected its own data harvesting form fields in the sites’ checkout pages.
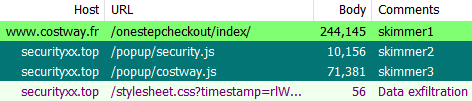
The second threat actor loaded the custom card skimmers from securityxx[.]top, one that directly collects data from the already present skimmer and the second which activates if the store is cleaned of the malicious code injected during the Magento 1 hack.
As Sophos highlights, the two threat actors installed three separate credit card skimmers after compromising Costway’s stores:
“A large number of Magento 1 sites have been hacked but yet are not necessarily being monetized,” Segura added.
“Other threat actors that want access will undoubtedly attempt to inject their own malicious code.
“When that happens, we see criminals trying to access the same resources and sometimes fighting with one another.”
Malwarebytes notified Costway that their stores were compromised and infected with credit card skimmers but their costway[.]fr website is still compromised.
Also Read: Website Ownership Laws: Your Rights And What These Protect
In September 2020, an automated hacking campaign targeting Magento sites successfully compromised roughly 2,000 online stores to steal credit cards.
The vast majority of them running Magento 1 software, out of support since June 2020 when it reached the end of support.
Such attacks have become a large enough problem that VISA issued an advisory urging merchants to migrate e-commerce sites to the more secure Magento 2.x software.
The U.S. Federal Bureau of Investigation (FBI) also issued a warning in October 2019 regarding e-skimming threats targeting both government agencies and SMBs (small and medium-sized businesses) that process online payments.
The FBI advises site owners to keep their software updated as one of the main mitigation measures against Magecart attacks.