KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Google Chrome now blocks access to websites on an additional seven TCP ports to protect against the NAT Slipstreaming 2.0 vulnerability.
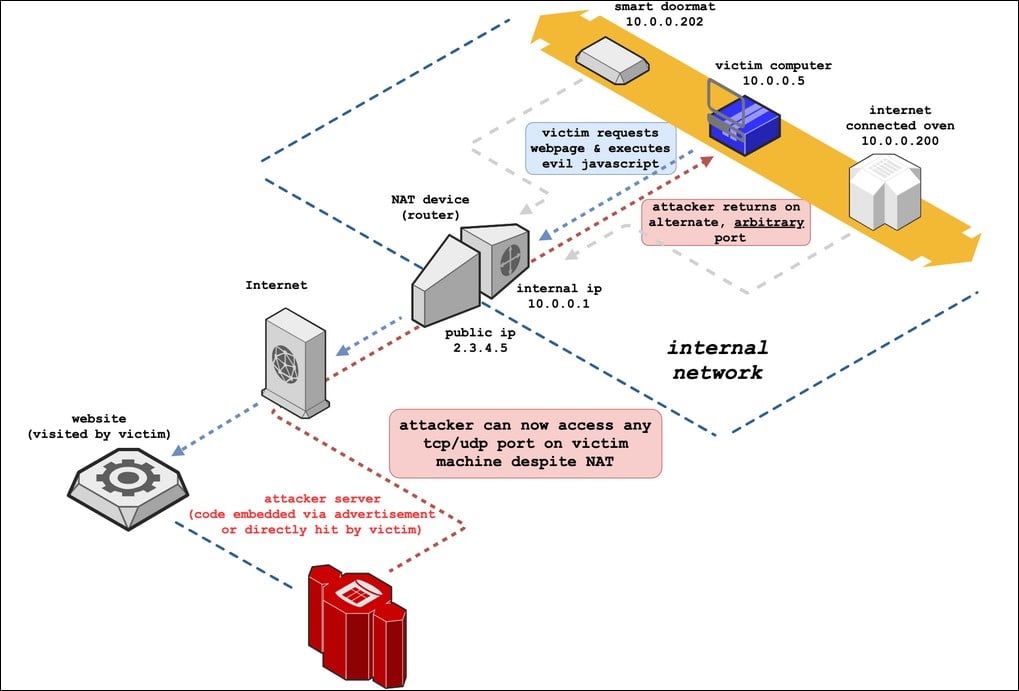
As a way to reduce the amount of public IP addresses and to increase security, a feature called Network Address Translation (NAT) is available in almost all routers and firewalls that allows devices using private non-routable IP address to still connect to the Internet.
This feature allows the router to track requests to the Internet from internal devices, and make the request for them on its own public IP address. When the remote computer responds, it will automatically forward the response back to the internal device that made the original request.
Also Read: Going Beyond DPO Meaning: Ever Heard of Outsourced DPO?
Last month, security researchers Sammy Kamkar and Armis researchers Ben Seri and Gregory Vishnipolsky disclosed a new version of the NAT Slipstreaming vulnerability.
This vulnerability allows a website to host malicious scripts that send a specially crafted response that bypasses the visitor’s NAT firewall to access any TCP/UDP port on the visitor’s internal network.
When the vulnerability was first disclosed, Google stated that they would block HTTP and HTTPS access to TCP ports 5060 and 5061 to protect against this vulnerability in the release of Chrome 87.
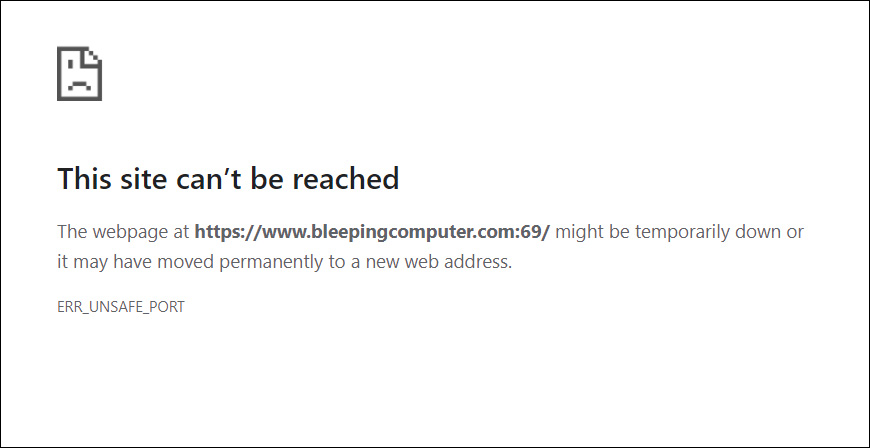
Today, Google announced that Chrome would also block HTTP, HTTPS, and FTP access to 69, 137, 161, 1719, 1720, 1723, and 6566 TCP ports.
“The NAT Slipstream 2.0 attack is a kind of cross-protocol request forgery which permits malicious internet servers to attack computers on a private network behind a NAT device. The attack depends on being able to send traffic on port 1720 (H.323).”
“To prevent future attacks, this change also blocks several other ports which are known to be inspected by NAT devices and may be subject to similar exploitation,” Google explains in the feature description on their Chrome Platform Status site.
When users attempt to connect to a website using these ports, Google Chrome will display a message stating that the site can’t be reached and showing an ‘ERR_UNSAFE_PORT’ error.
If you host a website running on these ports, you should switch to a different port to allow visitors to continue accessing your application.
Also Read: Limiting Location Data Exposure: 8 Best Practices
Firefox, Edge, and Safari 14.0.3 have already added mitigations for the NAT Slipstreaming vulnerability. While Edge will likely use the same ports as Chrome, it is not known what ports were blocked in Safari and Firefox.