KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Hackers hitting thousands of organizations worldwide in a massive phishing campaign forgot to protect their loot and let Google the stolen passwords for public searches.
The phishing campaign has been running for more than half a year and uses dozens of domains that host the phishing pages. It received constant updates to make the fraudulent Microsoft Office 365 login requests look more realistic.
Despite relying on simple techniques, the campaign has been successful in bypassing email protection filters and collected at least 1,000 login credentials for corporate Office 365 accounts.
Researchers at cybersecurity companies Check Point and Otorio analyzing this campaign discovered that the hackers exposed the stolen credentials to the public internet.
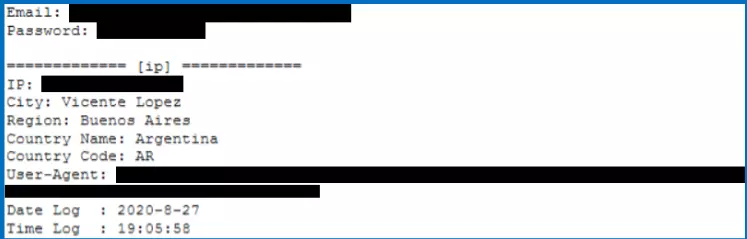
In a report published today, they explain that the attackers exfiltrated the information to domains they had registered specifically for the task. Their mistake was that they put the data in a publicly visible file that Google indexed.
As a result, Google could show results for queries of a stolen email address or password, as seen in the screenshot below:
Also Read: How to Send Mass Email Without Showing Addresses: 2 Great Workarounds
Researchers at the two cybersecurity companies say that the attackers also compromised legitimate WordPress servers to host the malicious PHP page delivered to victims.
“Attackers usually prefer to use compromised servers instead of their own infrastructure because of the existing websites’ well-known reputations,” the researchers explain.
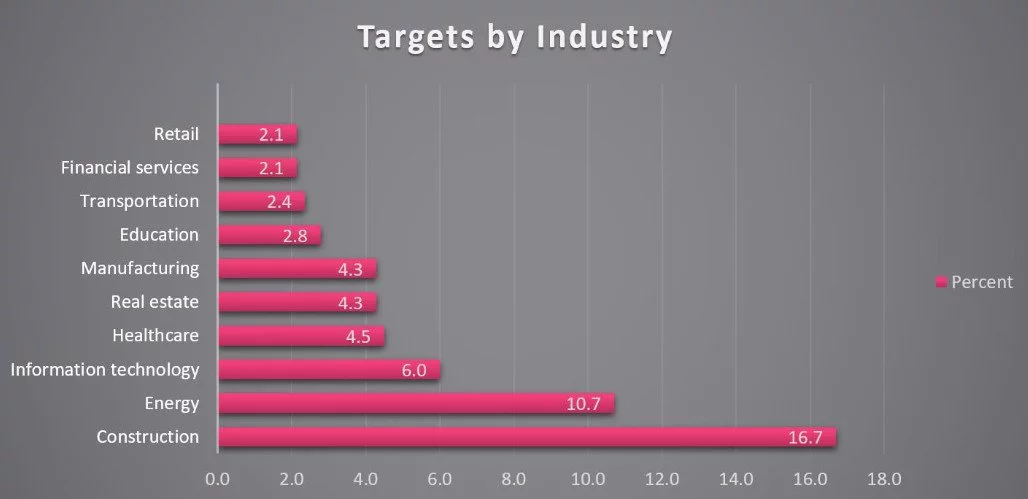
Processing information from about 500 entries, the researchers could determine that companies in the construction, energy, and IT sectors were the most prevalent targets of these phishing attacks.
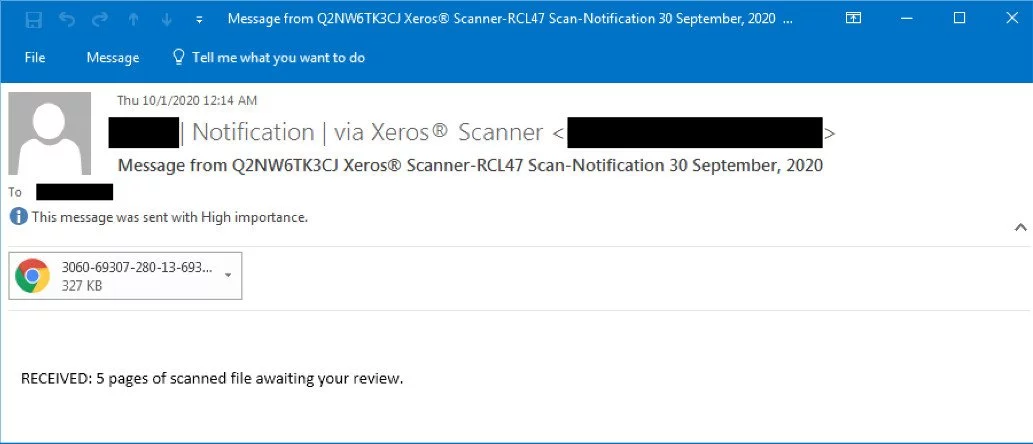
The attackers used several phishing email themes to lure potential victims into loading the landing page that collected their Microsoft Office 365 username and password.
The malicious emails had the target’s first name or company title in the subject line and purported to deliver a Xerox scan notification in HTML format.
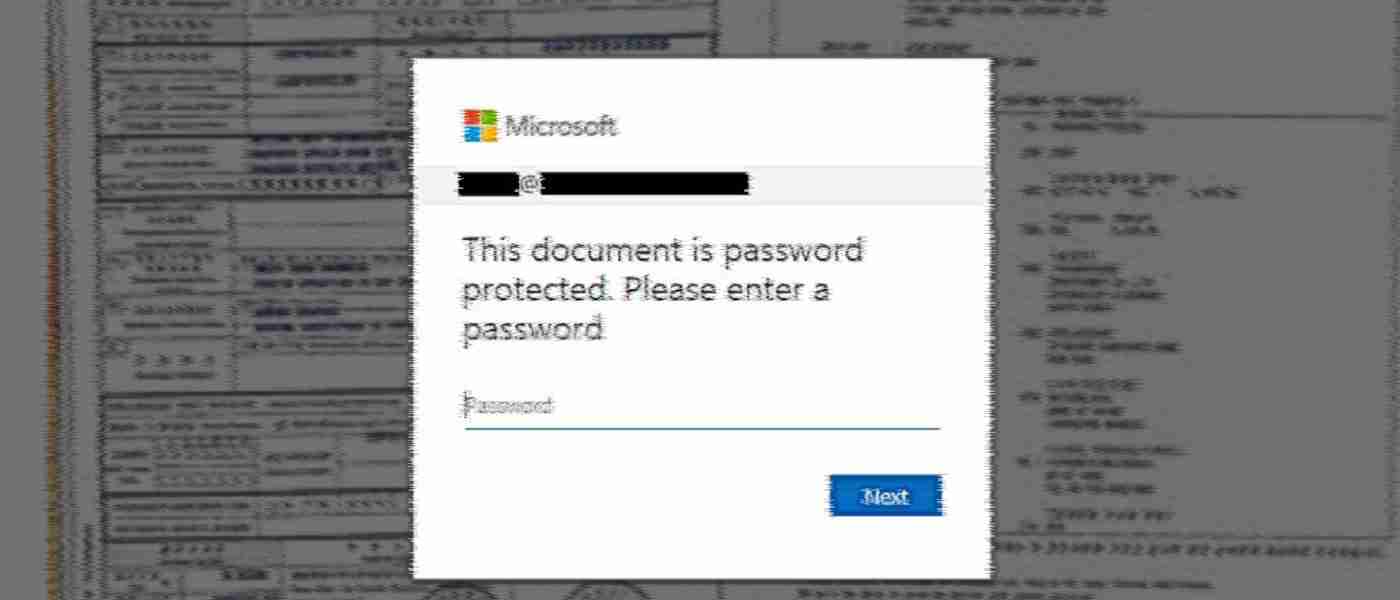
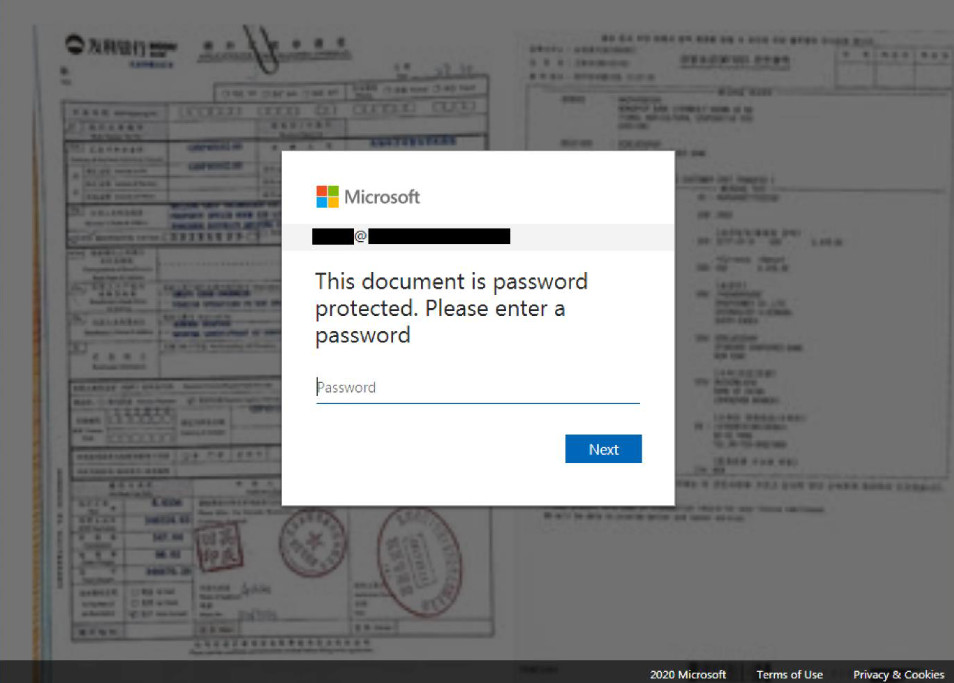
Opening the attachment loaded in the default web browser a blurred image overlaid by a fake Microsoft Office 365 login form. The username field is already populated with the victim’s email address, which typically removes suspicion of login theft.
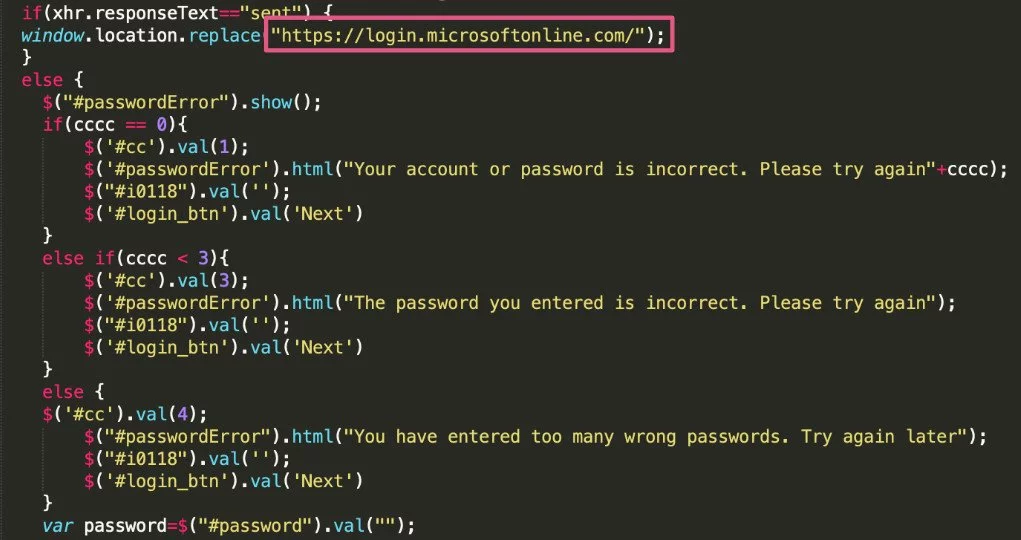
A JavaScript code running in the background checks the validity of the credentials, sends them to the attacker’s drop-zone server, and redirects the victim to the legitimate Office 365 login page as a distraction.
Also Read: How a Smart Contract Audit Works and Why it is Important
To keep the campaign undetected, the actor used compromised email accounts to distribute the fraudulent messages. For one attack, they impersonated the German hosting provider IONOS by 1&1.
Although this campaign started in August, the researchers found phishing emails from the same threat actor that dated from May 2020.
While Google indexing hackers’ pages where they save stolen data is not a first, it shows that not all malicious actors are sufficiently skilled to protect their operations. Even if they are not identified, at least their actions can be thwarted.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
