KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







GO SMS Pro, an Android instant messaging application with over 100 million installs, is publicly exposing private multimedia files shared between its users.
By abusing a flaw in the app, unauthenticated attackers can gain access to private voice messages, videos, and photos shared by GO SMS Pro users as Trustwave security researchers discovered three months ago.
The private media files sent by users to contacts who don’t have the app installed on their devices can be accessed from the app’s servers using a shortened URL which redirects to a content delivery network (CDN) server GO SMS Pro uses to store all shared files.
These shortened URLs are sequentially generated (using a hexadecimal counter) each time a file is shared between users and the media is stored on the CDN server.
This makes it very easy for anyone to go through all the private files shared by the app’s users, even without knowing any of the shared URLs.
Also Read: How a Smart Contract Audit Works and Why it is Important
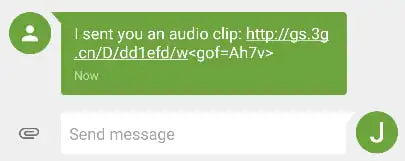
BleepingComputer was able to confirm the researchers’ findings by going through roughly two dozen such links and found photos of users’ cars, screenshots of other messages and Facebook posts, nude photos, videos, audio recordings, and even photos of sensitive documents.
Trustwave’s researchers said that it is trivial to create a simple script that would quickly generate a list of addresses linking to photos and videos shared using this vulnerable app.
“By taking the generated URLs and pasting them into the multi-tab extension on Chrome or Firefox, it is trivial to access private (and potentially sensitive) media files sent by users of this application,” they explained.
Trustwave disclosed the vulnerability 90 days after contacting the app’s developer on August 18 and after receiving no reply to three other emails sent in September, October, and earlier this week, in November.
BleepingComputer also reached out to the developer team using the email contact available on the app’s Play Store page but our messages also went unanswered.
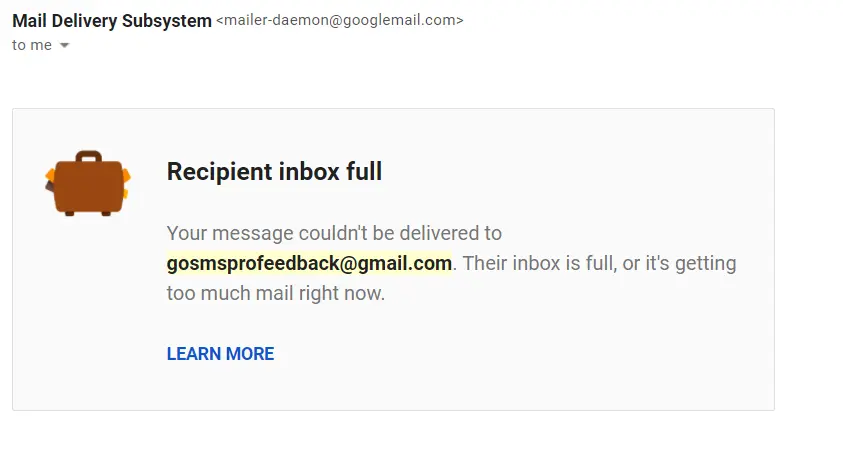
To make matters even worse, we were alerted that our email bounced either because the developer’s mailbox is full or because they are receiving way too many messages.
The developer’s website is not available at the moment, with customers who want to visit it seeing a Tengine web server successful installation message instead of the site’s contents.
Also Read: Data Centre Regulations Singapore: Does It Help To Progress?